What is Windows Pro Defence Kit?
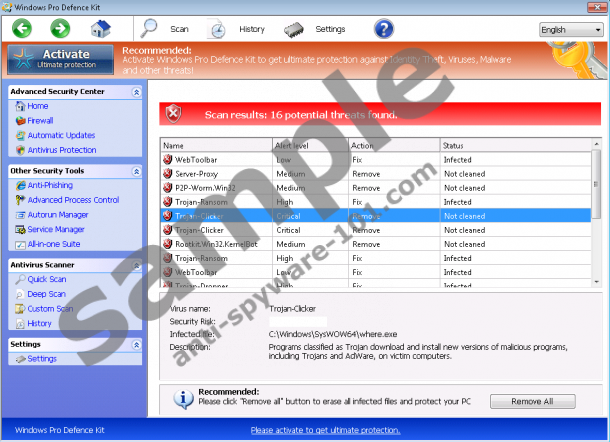
Windows Pro Defence Kit is a rogue anti-spyware program which you will definitely notice on your PC. It is installed without your knowledge, but once it is installed, it is impossible not to notice its scanner and recommendations to activate it. Windows Pro Defence Kit is aimed at convincing you that the computer is infected and that you need to invest in the program to have all those threats removed. Since the bogus security tool is not powered by any malware and spyware detection technology, it cannot identify and terminate malicious code. Visually, the application looks like a regular security tool; it contains icons typical of Windows operating system.

 100% FREE spyware scan and
100% FREE spyware scan and
tested removal of Windows Pro Defence Kit*
The truth is that Windows Pro Defence Kit is a scam, which replaces Windows Security Master, Windows Defence Unit, Windows Protection Booster, and other identical programs, all of which are called Rogue.VirusDoctor. When the computer is infected with one of the malware program attributed to the Rogue.VirusDoctor family, the removal of the program is a must, and the sooner you terminate the infection, the sooner you can fix the system.
What does Windows Pro Defence Kit do?
Windows Pro Defence Kit imitates system malfunctions to strengthen the impression that the system is being damaged by Trojan-Ransom, WebToolbar, P2p-Worm.Win32, and other threats. It blocks executable file so that you cannot launch existing programs and implement new ones. Moreover, it restricts your access to the Internet. You may also notice some start-up and shutdown problems and other system performance-related issues. In order to put an end to it, you should remove Windows Pro Defence Kit from the computer as soon as possible.
There is no need to spend up to $99.9 on the useless program because you can spend a much lower sum of money for a reputable spyware and malware prevention tool. Moreover, bear in mind that the remote attackers may be interested in your personal information, such as credit card details, your address, etc. If you want to protect your privacy and prevent identity theft, remove Windows Pro Defence Kit without hesitation.
How to remove Windows Pro Defence Kit?
Automatic removal is by far the easiest way to get rid of any malware and spyware program. Since Windows Pro Defence Kit is a complex application, and manual malware removal is cumbersome process, especially if you have no experience in it, we recommend that you implement a spyware removal tool. Windows Pro Defence Kit blocks executable files; hence, first you should activate the program with one of the following activation keys:
0W000-000B0-00T00-E0022
0W000-000B0-00T00-E0021
After activating the program, download and implement SpyHunter. This anti-spyware program can easily remove Windows Pro Defence Kit and safeguard the system against various computer threats. You will be protected against other rogue anti-spyware programs, browse hijackers, Trojan horses, etc.
In case the keys do not work, use the following removal guide:
How to terminate Windows Pro Defence Kit
- Restart the computer.
- Start tapping F8 once the BIOS screen loads.
- Select Safe Mode with Command Prompt.
- Press Enter.
- Type cd.. next to C:\Windows\system32\ and press Enter. .
- Type explorer.exe next to the C:\Windows line and hit Enter.
- Click Start.
- Click RUN/Search and type %appdata%.
- Press Enter.
- Delete the file svc-[random file name].exe.
- Restart the computer.
- Open the Start menu.
- Click RUN/Search.
- Enter regedit and hit Enter to access the Registry Editor.
- Go to HKEY_CURRECT_USER\Software\Microsoft\Windows NT\Current Version\Winlogon.
- Right-click the Shell and click Modify.
- Enter %WinDir%\Explorer.exe into the Value box and click OK.
- Now launch a browser and go to http://www.anti-spyware-101.com download-sph and download SpyHunter.
If you are determined to remove Windows Pro Defende Kit manually, you have to remove the following components. Bear in mind that you remove the rogue program at your own risk.
- Stop these processes:
- Delete the files of the rogue program:
- Remove the following registry entries:





0 Comments.