What is Windows Cleaning Tools?
Whether we like it or not, we have to face computer security issues every single day and Windows Cleaning Tools does not help with it at all. Even though it does sound like a reliable program, Windows Cleaning Tools is a direct clone of Windows Stability Maximizer, Windows Efficiency Reservoir, Windows Processes Accelerator and other programs from the Rogue.VirusDoctor batch of rogue antispyware, and it means that Windows Cleaning Tools is there to rob you and make your life miserable.
You most probably have got Windows Cleaning Tools while browsing the Internet, when you clicked on one of these online malware scanner advertisements. This rogue is very good at arriving at your system unnoticed and it is sure to attack you while you are the least expecting it by performing a fake system scan. During the scan Windows Cleaning Tools "detects" such infections as Virus.Win32.Sality, PSWTool or IM-Flooder, but these detections are not real, and Windows Cleaning Tools only wants to scare you into believing that your computer is severely infected and you need to "Activate Ultimate protection" otherwise you are doomed.
Note: Check your computer for Windows Cleaning Tools, download a reliable detection tool.
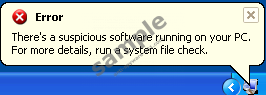
This impression is only reinforced by the fake security notifications that Windows Cleaning Tools makes pop up onto your screen every other minute:
Warning! Identity theft attempt Detected
Hidden connection IP: 58.82.12.124
Target: Your passwords for sitesError
Trojan activity detected. System data security is at risk.
It is recommended to activate protection and run a full system scan.Warning
Firewall has blocked a program from accessing the Internet
C:\program files\internet explorer\iexplore.exe
is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server.
Windows Cleaning Tools will also say that the infections have blocked your access to various programs (including the Internet browser), Registry Editor and Windows Task Manager. However, these symptoms belong to none the other, but Windows Cleaning Tools itself, because the rogue does that in order to avoid being removed.
Nevertheless, you can counter that by clicking the "Activate Ultimate Protection" button and entering this code:
0W000-000B0-00T00-E0020
Windows Cleaning Tools will be "registered" and all your programs and tools will be accessible again. Yet, it does not mean that the fight is over. The rogue will be dormant only for a short while and you need to delete Windows Cleaning Tools while it is regrouping. If you cannot terminate the rogue manually, you are advised to invest in a legitimate computer safeguard application that will perform a detailed systems can and erase Windows Cleaning Tools for good to the very last file.
100% FREE spyware scan andtested removal of Windows Cleaning Tools*




0 Comments.