What is Search.myradioxp.com?
Search.myradioxp.com is not a regular browser hijacker. This one is unlikely to corrupt your browsers without your permission. However, this search tool can change your browsers’ settings when you install software associated with it. Although this tool has an interface of a regular search engine, it certainly does not act like one. If you try using it as a regular search tool, you will find yourself redirected to a third-party page, such as search.yahoo.com. Unfortunately, some users ignore this “flaw” thinking that it is useless because of the links it provides. CNN, Salem Radio, Spotify, and Soundcloud are amongst the services that this strange hijacker provides links to. Do you enjoy having access to all of these services from one spot? Well you can easily attach links to them to your browser’s bar or a legitimate toolbar. You do not need some unreliable hijacker for it. In fact, we believe it is crucial to remove Search.myradioxp.com.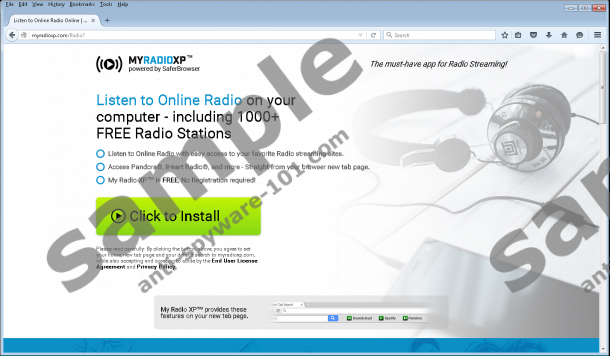

How does Search.myradioxp.com act?
Did you agree to install Search.myradioxp.com yourself or were you surprised to find it installed onto your browsers? Our analysts at Anti-Spyware-101.com inform that this hijacker is identical to other unreliable hijackers, including Search.mycurrentnewsxp.com and Search.mydailyversexp.com. All of these unreliable search tools have their own extensions that activate them. In our case, it is the My Radio XP by SaferBrowser extension that users can install from myradioxp.com or from a Chrome web store page at chrome.google.com/webstore/detail/my-radio-xp/ijinnpmmaakgiepakhpjdbmmlnapkpmp. The random collection of letters, ijinnpmmaakgiepakhpjdbmmlnapkpmp, actually reveals the Chrome ID for this strange extension. This is the ID you need to keep in mind if you want to find the folder carrying all of the files associated with this infection, as this folder’s name is the ID itself. Firefox users will identify this add-on by the file called “radio@jetpack.xpi”. Keep in mind that it will not be enough to remove a few files to completely eliminate this extension and the hijacker associated with it.
It is not surprising that computer users install Search.myradioxp.com. First of all, this search tool looks authentic. Secondly, many users are very careless when downloading unreliable software onto their computers. Most do not even check the Privacy Policy, which, in our opinion, should be the first thing to do. After analyzing this document we now know that the hijacker can collect private information and share it with unknown parties. If all computer users were aware of this, we are sure that they would stay away from this infection. Of course, we also need to consider the possibility of this hijacker taking over your browsers without your permission. Needless to say, software capable of infecting computers illegally is malicious, and should not be trusted. Even if this hijacker appears to offer some beneficial tools, it is an invader that should be eliminated without further hesitation. The good news is that this hijacker is not extremely complex, and it is quite easy to get rid of it.
How to eliminate Search.myradioxp.com
Users are quick to install malware, but they often postpone the necessary removal processes because they do not know how to proceed. In order to delete Search.myradioxp.com you need to perform a few different steps. First of all, eliminate the extension associated with this hijacker. In some cases, this will be enough to get rid of the hijacker as well. Unfortunately, it is also possible that you will need to modify search settings manually. Do not worry if this operation is foreign to you because the guide below walks you through it one step at a time. In fact, removing this hijacker is the easy part. The difficult part is cleaning your operating system and protecting it from further attacks. If you cannot guarantee that you will eliminate all threats successfully or reliably reinforce Windows protection, it is best to employ anti-malware software. Considering that this hijacker could run along with other threats, this is your best option.
Removal Guide
Windows 10 or Windows 8:
- Launch RUN, enter Control Panel, and click OK.
- Navigate to Uninstall a program.
- Right-click the undesirable application and select Uninstall.
Windows 7 or Windows Vista:
- Click the Windows/Start menu icon on the Taskbar.
- Open the Control Panel menu and click Uninstall a program.
- Right-click the undesirable application and select Uninstall.
Windows XP:
- Click the Start menu icon on the left of the Taskbar.
- Open Control Panel and double-click Add or Remove Programs.
- Select the unwanted program and click Remove.
Mozilla Firefox:
- Open Firefox and tap Alt+T.
- Select Add-ons and move to the Extensions list.
- Remove the unwanted extensions.
- Tap Alt+T again.
- Select Options and move to the General menu.
- Overwrite the provided Home Page URL.
- Move to the General menu.
- Remove the unwanted search provider.
Internet Explorer:
- Open IE and tap Alt+T.
- Select Manage Add-ons and move to Search Providers.
- Select the preferred provider.
- Remove the unwanted search provider and click Close.
- Tap Alt+T again and select Internet options.
- Click the General tab, overwrite the Home Page URL, and click OK.
Google Chrome:
- Open Chrome and tap Alt+F.
- Select More tools and move to Extensions.
- Click the trash bin button and choose Remove.
- In the menu on the left click Settings.
- Go to On Startup and choose Open a specific page or set of pages.
- Click Set pages and overwrite the undesirable option.
- Go to Search and click Manage search engines…
- Choose the preferred search provider.
- Click X to remove the unwanted provider and click Done.
N.B. this hijacker creates registry entries that you need to eliminate as well. If you have never dealt with the Registry Editor, this task might be a little complicated for you, but we are sure that you will be successful if you perform every step with caution. If you are having issues, contact us by leaving a comment below.
- Launch RUN (tap Win+R).
- Enter regedit.exe and run it as administrator.
- In Registry Editor follow the path to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\.
- Right-click and Delete these keys: My Email XP_RASAPI32 and My Email XP_RASMANCS.
tested removal of Search.myradioxp.com*





0 Comments.