What is File-help@india.com Ransomware?
Users who see a window opened on their screens claiming that security vulnerability has been discovered in their networks should know that File-help@india.com Ransomware has sneaked onto their computers illegally and opened this HOW TO DECRYPT YOUR FILES window for them. Therefore, users should completely ignore the message they see provided for them. Users should not pay the required money to cyber criminals either. It is highly advisable to go to delete File-help@india.com Ransomware the first thing. Deleting it from the system will not be a very easy task because it is quite a serious computer infection which does not have an uninstaller. Luckily, it does not drop any .exe files on computers, does not make modifications in the system registry, and does not block system utilities, so users should be able to erase this threat manually after reading this article.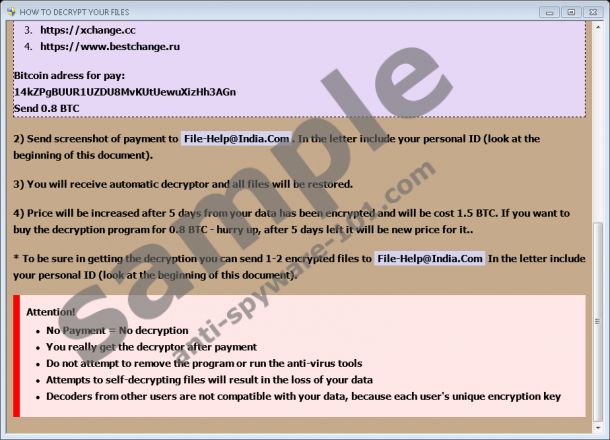


What does File-help@india.com Ransomware do?
File-help@india.com Ransomware, just like other similar infections, seeks to obtain money from people. Even though users are told that their files have been encrypted due to “serious vulnerability in your network security”, the truth is that this ransomware infection has locked personal files so that it could easily convince users to pay money. Users are asked to pay 0.8 Bitcoin (~ 1000 USD) to get an automatic decryptor. They have to do that within 5 days if they do not want the price to double. After making a payment, users have to send screenshots as a proof of payment and a unique ID provided on the ransom note to File-Help@india.com. In order to show users that they can really decrypt files for them, cyber criminals are ready to decrypt 1-2 files for free. You can send those two files to get them decrypted, but it is not recommended to transfer money to cyber criminals by any means. There are no guarantees that the [random symbols].[file-help@india.com].mails extension will be removed from files and, consequently, they will be decrypted after sending money. There are, actually, many cases when users do not get anything in return after paying a ransom, but, of course, you are the one who can make a final decision. If you make a decision to keep 1000 USD in your pocket, do not hurry to delete those encrypted files – you might be able to unlock them with a free decryptor specialists might develop in the future. Of course, you cannot let File-help@india.com Ransomware stay on your system.
As has already been mentioned in the first paragraph of this article, File-help@india.com Ransomware differs from other ransomware infections making a bunch of modifications on the affected computer. The only file it drops is how to recover encrypted files.hta, which is responsible for displaying a window with a ransom note on users’ Desktops. The ransomware infection itself works from the place it has been launched by a user, usually %USERPROFILE%\Downloads or %USERPROFILE%\Desktop. The file which launches this threat has a random name, so finding and deleting it is quite a challenge.
Where does File-help@india.com Ransomware come from?
Not much is known about the dissemination of File-help@india.com Ransomware, but it is very likely that it is spread through spam emails as other ransomware infections using @india.com emails do. More specifically, these infections travel as attachments in these emails. Of course, users are not told that an email they see contains malware. In most cases, a malicious attachment is disguised as an important document, which explains why so many users open these attachments without fear and, consequently, allow malicious software to enter their computers. Spam emails are, actually, only one of the ways ransomware infections are spread. It is known that these computer infections might be hiding on dubious third-party pages too. Finally, malware already existing on the computer might help other infections to enter the system too. As a consequence, users whose PCs are connected to the Internet should go to acquire a security application. It is, of course, not enough to download security software only. It needs to be enabled too.
How do I uninstall File-help@india.com Ransomware?
The removal of File-help@india.com Ransomware should not be very a very complicated procedure because you only need to find and erase two files: a recently downloaded malicious file and how to recover encrypted files.hta. You should be able to find a .hta file on Desktop, whereas the malicious file you have downloaded should be located in the Downloads folder. If you cannot find it or simply wish to erase File-help@india.com Ransomware quicker, use SpyHunter. Do not forget that an automatic malware remover is not capable of unlocking the personal data encrypted by ransomware either.
Remove File-help@india.com Ransomware manually
- Open the Windows Explorer by pressing Win+E simultaneously.
- Type %USERPROFILE%\Desktop in the URL bar at the top and press Enter.
- Locate how to recover encrypted files.hta and delete it.
- Go to %USERPROFILE%\Downloads.
- Delete all suspicious recently downloaded files.
- Empty the Recycle bin.
tested removal of File-help@india.com Ransomware*





0 Comments.