What is Cyberresearcher Ransomware?
Malware developers are constantly on the look on how they can exploit Internet users, and make quick, illegal profits. For the past few years, their favorite tool to do so has been ransomware applications. Researchers at Anti-Spyware-101.com have discovered yet another program of this classification, and it goes by the name of Cyberresearcher Ransomware. If you ever cross paths with it, you must do everything in your power to refrain from it at all times. Doing so is vital because this malware, like its counterparts, is designed to encrypt vast quantities of data without any notification or authorization. As you can imagine, having this ransomware up and running on your computer could lead to devastating consequences. In our report, you will find further information regarding its intricate inner workings. Additionally, we include a few virtual security tips alongside a detailed removal guide, which you should use to delete Cyberresearcher Ransomware once and for all.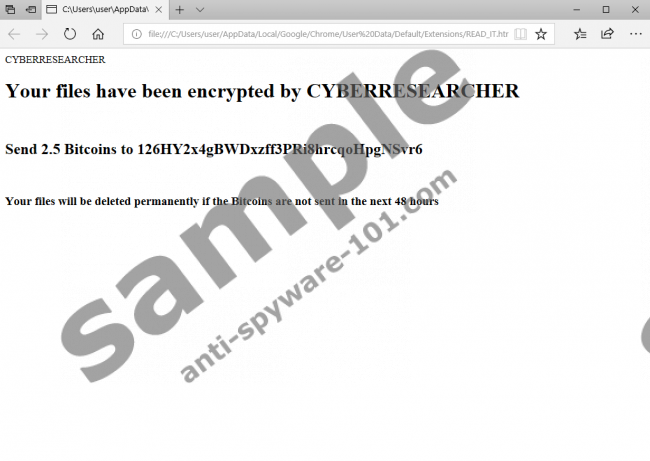
What does Cyberresearcher Ransomware do?
Right away, our malware experts have discovered that Cyberresearcher Ransomware happens to be yet another malicious application crafted using the notorious Hidden-Tear project. Thus, it is not at all surprising that the malware in question is related to other ransomware applications that are based on this devious project. Just like its counterparts, it starts doing its dirty work as soon as it gains access to your operating system. To determine which files it will lock, this ransomware scans your hard drive. Right after that, it starts the encryption process. Unfortunately, this malware blindsides most users that are affected by it since it functions silently. During encryption, your data is locked with a robust algorithm, which means that manual decryption is out of the question. Upon further analysis, our researchers have noticed that this ransomware does not encrypt files, which are essential for your operating system's functionality. However, it still locks a vast majority of other data. Because of that, you could lose the ability to use quite a few of your applications since data needed for their inner workings will be unusable. As soon as this ransomware is done with the encryption, it issues a ransom note, which informs you about what has happened. Also, it asks for a ransom in return for decryption services. It is essential to note that paying a ransom could be a waste of money since malware developers are not legally bound to provide such services even you abide by their demands. Make no mistake, and remove Cyberresearcher Ransomware as soon as it is found up and running on your operating system. You can do so in just a few simple steps by using our detailed instructions below.
How to improve your virtual security
If you wish to have a clean and secure operating system at all times, be sure to take preventative measures to improve your overall virtual security. Doing so is essential since the Internet is full of threats, to put it lightly. First, we urge you to start practicing safe browsing habits. Our researchers recommend refraining from all unauthorized download sites since they are infamous for hosting bundled installers, which malware developers tend to use for distribution purposes. Likewise, you should know that cyber crooks often use spam email campaigns for distribution purposes. Thus, we advise you not to download any email attachments that come your way from unknown sources as that could prove to be a malicious .exe file. Also, malware developers often use hoax advertising campaigns to trick naive Internet users into downloading their invasive applications. If you want to limit your chances of infecting your PC in such a way, you must always learn about a program that you want to have active on your PC beforehand. Lastly, but most importantly, be sure to install a professional antimalware tool, if you do not have one already. Such a tool is the most important part of your virtual security because it can identify and remove any devious application automatically.
How to remove Cyberresearcher Ransomware
Removal of Cyberresearcher Ransomware should be your utmost priority if it is already up and running on your PC. Use termination instructions with care since a single mistake during this procedure could have detrimental consequences. In some instances, traces of Cyberresearcher Ransomware could act deviously, to put it lightly. For example, just a few leftovers might be enough for this malware to continue doing its dirty work. Also, those same traces could be used to restore Cyberresearcher Ransomware without your knowledge. If you want to be sure that the removal process has been successful, make sure to double-check your entire operating system for anything associated with this ransomware. Alternatively, you can scan your computer with a reliable antimalware tool because it can detect and delete anything linked to Cyberresearcher Ransomware automatically.
How to remove Cyberresearcher Ransomware from your PC
- Right-click your Task Bar.
- Select Start Task Manager.
- Click the Processes tab.
- Select the malicious process and click End Process. Note that the name of this process is random.
- Open your File Explorer.
- Go to C:\Users\[your username]\Downloads.
- Select the malicious .exe file and tap Delete on your keyboard. The name of this file is random. Note that it should be the same name as the malicious process.
- Go to C:\Users\[your username]\AppData\Local\Temp.
- Select the malicious .exe file and tap Delete on your keyboard. The name of this file is random. Note that it should be the same name as the malicious process.
- Close your File Explorer.
- Right-click the Recycle Bin and select Empty Recycle Bin.
100% FREE spyware scan and
tested removal of Cyberresearcher Ransomware*
Stop these Cyberresearcher Ransomware Processes:





0 Comments.