What is Crypt0 Ransomware?
A new ransomware infection Crypt0 Ransomware has been detected recently by specialists at anti-spyware-101.com. It has been immediately put into a category of ransomware infections because researchers have found out that it encrypts personal files within a few seconds. It seems that Crypt0 Ransomware is created by amateurs, and it should not become very popular; however, it is still a threat to files users keep on their computers because it can really lock them with the RSA-2048 encryption. Of course, there is a reason why it acts this way – cyber criminals have created Crypt0 Ransomware to encrypt users’ files in order to be able to extort money from them easily. Even though it is not written anywhere that the file decryptor is not free, you will definitely be offered to make a payment to get the decryptor if you contact cyber criminals by writing an email to fndimaf@gmail.com. To be frank, it is a bad idea to transfer money cyber criminals require because the decryptor might not even be sent to you, but, of course, your money will be taken. In addition, specialists have developed a free decryptor recently, which means that there is a possibility to unlock files without the private key cyber criminals own.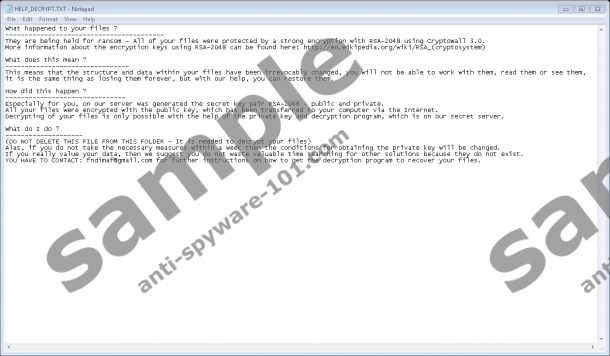
What does Crypt0 Ransomware do?
The main goal of Crypt0 Ransomware is to lock files so that cyber criminals could offer users to purchase a decryptor. Therefore, it encrypts personal files it finds on the computer the second it enters the system. Fortunately, it does not encrypt system files in the %WINDIR% directory, so it should not lock any files that have the Microsoft signature too. You will find out quickly which of your files are encrypted and which are not because _crypt0 will be added next to the original file name after the encryption, for example, the name of the document.txt file will be changed to document_crypt0.txt. Once this infection finishes encrypting files, it creates the HELP_DECRYPT.txt file in every directory containing encrypted data. If you open it, you will see a text telling that all personal files “are being held for ransom”, and “the conditions for obtaining the private key will be changed” if you do not contact cyber criminals within a week. Believe us; the price of the decryptor is high, so you should not even bother writing an email if you are not planning on paying money to cyber criminals. What you should do instead is to delete Crypt0 Ransomware fully and then use the free decryptor you can find on the web. Alternatively, users who have a backup of their major files can restore them without the special tool or decryption key. Of course, they also need to delete the ransomware infection from their computers first.
The executable file of the ransomware crypt0-Encrypt.exe is dropped into %ALLUSERSPROFILE%\Start Menu\Programs\Startup (Windows XP) or %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup (Windows Vista and later) when Crypt0 Ransomware enters the computer. These folders are called points of execution (POE) of Crypt0 Ransomware. To be more specific, this means that the ransomware infection will launch again automatically after the system restart and encrypt your files again. This will happen with every system restart unless you fully delete Crypt0 Ransomware, which is why we suggest that you do not postpone its removal.
Where does Crypt0 Ransomware come from?
Crypt0 Ransomware is distributed exactly like other ransomware infections recently developed by cyber criminals, e.g. Flyper Ransomware, Seven_legion@aol.com Ransomware, and RansomCuck Ransomware. This is, it is spread through spam emails. The executable file of the ransomware (crypt0-Encrypt.exe) is dropped on the computer once the spam email attachment is opened. Unfortunately, many users open it without fear even though they know that attachments spam emails contain might cause serious harm to their computers. They do that because the malicious attachment is made to look harmless. We do not blame those users, but we suggest staying away from the spam mail folder in the future in order not to allow any other computer infection to enter the system.
How can I delete Crypt0 Ransomware?
To fully delete Crypt0 Ransomware from your computer, you will have to remove the executable file crypt0-Encrypt.exe from the POE directory. You will find instructions that will guide you through the process below this report. If the manual method is not for you, you can get rid of the ransomware infection in an automatic way. In order to do that, you will have to acquire SpyHunter. Users who have this scanner installed on their PCs have to reinstall it too if they wish to use it because it is very likely that it has been locked by Crypt0 Ransomware and is no longer effective.
The manual Crypt0 Ransomware removal instructions
- Launch Explorer (Win+E).
- Open %ALLUSERSPROFILE%\Start Menu\Programs\Startup if you use Windows XP.
- Open %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup if you use Windows Vista, 7, 8, 8.1, or Windows 10.
- Locate the file crypt0-Encrypt.exe.
- Delete it.
- Remove HELP_DECRYPT.txt from directories containing encrypted files.
- Empty the Recycle Bin.
tested removal of Crypt0 Ransomware*





0 Comments.