What is CryLocker Ransomware?
The new nightmare that can hit your computer silently but rather deadly is called CryLocker Ransomware. This malware infection has a similar name to another ransomware that showed up a few weeks ago, Cry Ransomware, but they seem to be different in several areas. Nevertheless, their ransom note is practically identical. According to our malware researchers working at anti-spyware-101.com, this can happen when authors simply copy another threat or these infections come from the same source, i.e., a ransomware service offered on the Dark Web. We believe that the latter in more likely in this case as even the used personalized websites are all the same apart from the money extorted from the victims, of course. This ransomware encrypts most of your files with an algorithm that is virtually impossible to crack; therefore, it is quite possible that you will not be able to recover your files after this serious attack. We do not advise you to pay the demanded fee because in most cases this is just a scam and you will not get anything in return. If you want to know how you can remove CryLocker Ransomware from your system and how you can avoid similar dangerous threats, please read on.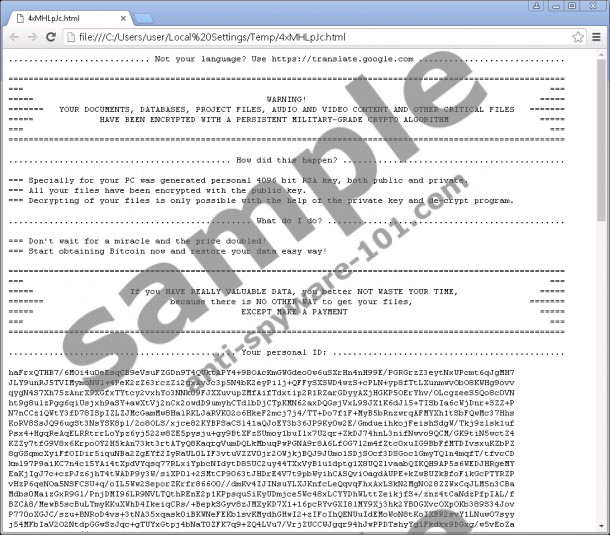


Where does CryLocker Ransomware come from?
Initially, this threat started to spread using Rig Exploit Kit and after a few days also by Sundown Exploit Kit. This simply means that the cyber criminals behind this malicious attack rely on the exploitation of outdated software on the victims’ machines. In other words, if your browsers and your drivers (Java, Flash, and QuickTime) are not up-to-date, previous bugs and security holes can be exploited to drop this infection onto your computer. This is usually done through webpages specifically designed for infecting your system with dangerous malware such as CryLocker Ransomware. You may think that you would never visit such a site. So let us tell you how it is still possible.
First, there could be malware programs hiding on your system, such as browser hijackers and ad-supported applications. These infections are capable of introducing you to unreliable web content like third-party advertisements and sponsored links. If you click on any of these, you may be redirected to a malicious site containing malicious Flash or Javascript code. The moment this page loads in your browser, this code runs and infects your computer. You will not even realize this until the moment your files become inaccessible and the ransom note image locks your screen. Second, this can also happen when you are viewing an unfamiliar gaming or file-sharing website because these are usually full of unreliable third-party ads. Although you may not be able to recover your files after this attack, you should definitely remove CryLocker Ransomware if you want to restore your system security.
How does CryLocker Ransomware work?
This malware program targets over 650 file extensions, which means that all of your photos, videos, music files, databases, archives, and other third-party program files can be lost in this encryption spree. Once this infection encrypts your files, a “.cry” extension is appended to them. After the job is done, your desktop wallpaper gets replaced by its own image, which is a ransom note. This message tells you to open one of the ransom note text files that are dropped onto your desktop for more information about this attack and how you can get your files back. This image ends with an Albert Einstein quote at the bottom that goes: “Some people cry over their fate and some people buy their happiness.”
Both of the ransom note files are rather long and detailed. You are informed that you have to visit a website that is set up for you personally. You have to use the given unique ID to log in to this website. Upon login you may feel a bit frightened as this site looks like a legitimate official site for a supposed “Central Security Treatment Organization,” whose logo also looks quite convincing. In order for you to trust these criminals, a chance is offered to you on this site to decrypt one of your files. However, our research revealed that this feature may not even work properly. So you had better make sure that it does before you rush to pay the fee.
While the aforementioned Cry Ransomware infection demanded 93 USD, these crooks seem to have aimed “a bit” higher as they want 625 USD in exchange for the private key and the decryption tool. This is a lot of money. Therefore, you need to be careful how you decide. We cannot claim that there is no chance for you to get this key and the tool if you pay up. But there can be complications; and, also, let us not forget about the fact that you have been attacked by these cyber criminals. What if they shut down the remote server that stores your private key or simply, the connection breaks up? How would you feel to realize that you just wasted 625 dollars on nothing? This is really not an easy decision. Nevertheless, we advise you to remove CryLocker Ransomware ASAP.
How do I delete CryLocker Ransomware?
There is, of course, one way for you to be on the safe side, apart from your operating system’s language set to Belorussian, Kazakh, Russian, Sakha, Ukrainian, or Uzbek, in which case this ransomware does not seem to encrypt your files. If you regularly make backup copies onto a removable hard disk or Flash drive, you can easily restore those files. But do not rush with the recovery because first you need to delete CryLocker Ransomware and make sure that your computer is completely clean of any malicious programs. If you want to take down this ugly beast manually, you can follow our guide below. Hopefully, this attack made you realize that you need to be more careful where you click and what kind of websites you land on. But, if you are looking for decent protection for your computer, you should consider employing a reputable anti-malware application.
Remove CryLocker Ransomware from Windows
- Tap Win+E to open File Explorer.
- Bin the attached file you downloaded from the spam.
- Delete the following files:
%UserProfile%\AppData\Local\Temp\[random_characters].exe
%UserProfile%\AppData\Local\Temp\[random_characters].tmp
%UserProfile%\AppData\Local\Temp\[random_characters].html
%UserProfile%\Desktop\!Recovery_[random_characters].html
%UserProfile%\Desktop\!Recovery_[random_characters].txt
%UserProfile%\Desktop\old_shortcuts\
C:\Windows\System32\Tasks\[random_characters]
C:\Temp\lol.txt - Empty your Recycle Bin.
- Tap Win+R and type regedit. Click OK.
- Remove “HKCU\Software\[random_chars].exe” registry key.
- Exit the editor.
- Restart your computer.
tested removal of CryLocker Ransomware*





0 Comments.