What is Additionalsearch.co.uk?
Additionalsearch.co.uk is a site that has an interface of a search engine. The search box in the middle indicates that search results can be produced. Also, the site provides a number of links that all represent different bbc.co.uk articles. Additionally, links to the bbc.com/weather weather forecast are included as well. At first sight, this search engine looks completely normal. It is when you take a better look that you realize something is not right. For one, we do not have access to the Privacy Policy or any other legal document that would reveal important information about the hijacker, and that cannot be ignored. If this information is not provided – and we do not have an official download site to fall back onto either – there is a possibility that the creator of the search tool is trying to hide something. If that were the case, your virtual security could be at risk just by using this seemingly reliable search tool, and this is why we discuss its removal. We can show you how to delete Additionalsearch.co.uk from your browsers.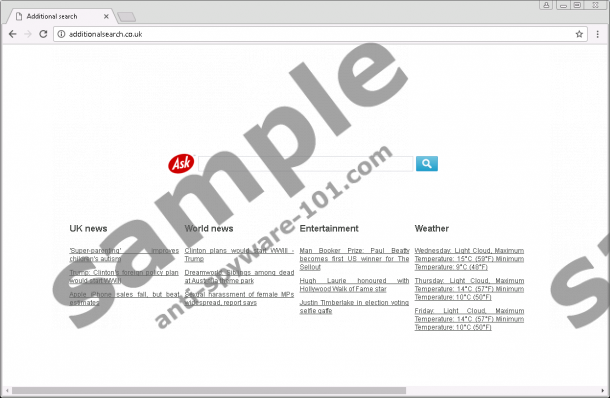
How does Additionalsearch.co.uk work?
It is truly unnerving that Additionalsearch.co.uk has chosen to conceal information about its activity. Due to this, we cannot even trust the search results that it shows via uk.ask.com. Speaking of this search engine, although there is an Ask logo next to the search dialog box, we cannot claim that the results shown are trustworthy. Also, search tools capable of automatically redirecting to third-party sites without permission are often considered intrusive and malicious. Although uk.ask.com is generally known as a reliable and trustworthy search engine, you must have noticed that it shows ads. Even if it is not influenced by a browser hijacker, this search tool displays advertisements, but the problem is that we do not know if Additionalsearch.co.uk cannot inject its own ads. Just because we do not know anything about this search tool, we have to assume that maybe it works with unreliable advertisers who pay money to have their offers promoted at the top of every search results page. Considering that there are plenty of malware distributors who spread infections via ads, we have to think about the removal of this search tool.
When you interact with the suspicious Additionalsearch.co.uk, you might let in tracking cookies. The hijacker might be able to install third-party cookies as well, which means that there might be several different suspicious parties spying you at the same time. Whether or not your personal information is at risk, we do not know, but it is wise to assume the worst, considering that we actually do not know much. The suspicious data-tracking tools might also be employed by third-party malware. Where does it come from? According to our malware researchers, Additionalsearch.co.uk might be spread by third-party installers that bundle multiple programs together. Considering that there are a lot of malicious installers, it is sensible to consider that maybe malicious infections have been packaged along with this hijacker as well. Do not waste time inspecting your operating system and identifying malware yourself. Instead, install a trusted malware scanner that will have no trouble identifying the real threats. This step is exceptionally important if you choose to get rid of all threats active on your PC in a manual manner.
How to delete Additionalsearch.co.uk
Do not hesitate for a moment about the removal of Additionalsearch.co.uk. This search tool might look okay, but it is too much of a wild card to trust. Sure, there are search tools we cannot trust that provide us with legal information, but the absence of it raises too many questions. So, if you are installing a search tool (or if an unfamiliar search tool hijacks your browsers), the first thing you must do is check the legal information. Afterward, do some research or, if you do not have time, install a malware scanner to examine the operating system and inform if malicious threats have invaded your PC. We advise implementing anti-malware software to erase all threats and clean your PC, but we have created a guide that will assist you with the manual elimination of the hijacker. But keep in mind that your operating system and browsers will remain vulnerable until you employ reliable security software, which is why we suggest using anti-malware software.
Removal Instructions
Mozilla Firefox:
- Tap Win+E keys simultaneously to open the Explorer window.
- Type %AppData%\Mozilla\Firefox\Profiles\ into the address bar.
- Open the folder that represents your Firefox profile (random characters) and then open the prefs.js file.
- Locate the URL of the hijacker and replace it with the preferred URL.
- Save the file and then immediately perform a full system scan to check for leftovers.
Internet Explorer:
- Tap Win+R keys simultaneously to launch the RUN dialog box.
- Navigate to [HKLM/HKCU]\Software\Microsoft\Internet Explorer\Main.
- Double-click the Start Page value to open the Edit String dialog box.
- Locate the URL of the hijacker and replace it with the preferred URL.
- Click OK and then immediately perform a full system scan to check for leftovers.
Google Chrome:
- Tap Win+E keys simultaneously to open the Explorer window.
- Enter %UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\ into the address bar if you are on Windows XP, or %LOCALAPPDATA%\Google\Chrome\User Data\ for all other Windows versions.
- Open the Default folder. Note that if there are multiple profiles on your Chrome browser, you will have to open the folder that represents your Profile folder.
- Open the file named Preferences.
- Overwrite the hijacker’s URL and save the file.
- Open the Secure Preferences file and repeat step 5.
- Immediately perform a full system scan to check for leftovers.
tested removal of Additionalsearch.co.uk*





0 Comments.