What is Windows Secure Web Patch?
Beware of Windows Secure Web Patch, because this fraudulent application wants you to expose your personal sensitive information to its creators. You are expected to “purchase” the full version of the rogue which supposedly removes various infections of the system. You cannot trust this application because it is a clone of such malware as Window Instant Scanner, Windows Privacy Counsel, Windows Custom Safety and others which belong to Rogue.VirusDoctor family. Judging from the name of the rogue, Windows Secure Web Patch seems to be a legitimate Windows product; however, this is just a trick to gain your trust. The malware is absolutely worthless; therefore, remove it at once. Deletion of the rogue is highly recommended, because only when the rogue is removed, you can use the computer as usual.
The presence of Windows Secure Web Patch in the system means that the rogue will manipulate you. The malware disorders the system to make you think that you have caught harmful infections such as Trojans, worms, key loggers, etc. There is no need to panic, because such infections do not exist even if this malware claims so. When the rogue is present in the system, some executable files might be non-responsive. For example, when you attempt to launch a security tool, the rogue blocks it so that the application cannot detect and remove it. Moreover, the rogue disables your Internet connection so that you cannot find any useful information on removal of the rogue or download a removal tool. Registry Editor, where the key changes are made, and Task Manager, which shows the processes of the system, are hidden from users. When these come into one, it becomes a challenge to get rid of the infection.
100% FREE spyware scan and
tested removal of Windows Secure Web Patch*
Besides threatening you with simulated disorders of the system, Windows Secure Web Patch struggles to make you think that it is the best antivirus software you have ever had. It “scans” the system and presents “threats”, which you are expected to be afraid of, and which should force you to purchase the full version of Windows Secure Web Patch . The malware also produces imaginary notification which, as well as bogus infections should be ignored. The rogue will use the notifications provided below:
Error
Potential malware detected.
It is recommended to activate protection and perform a thorough system scan to remove the malware.Warning! Virus Detected
Threat detected: FTP ServerError
Keylogger activity detected. System information security is at risk. It is recommended to activate protection and run a full system scan.
The three notification given are not the only bogus messages that you will receive from the rogue. Windows Secure Web Patch display loads of warnings and errors to make you think that the system is at risk. Ignore the notifications, ignore the threats presented by the rogue, and, lastly, remove Windows Secure Web Patch from the system.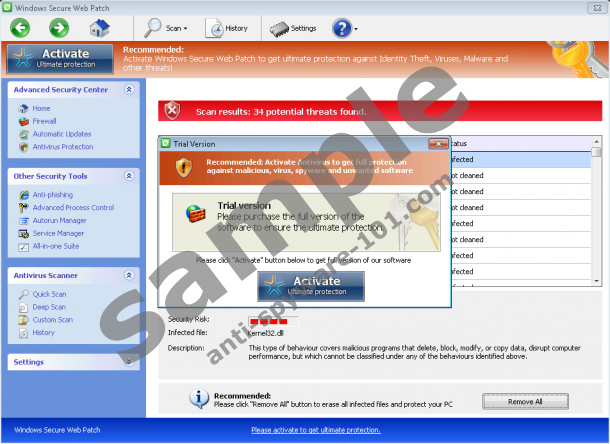




Warning, this parasite will block your Internet connection. Click here for instructions how to renew your Internet access.
Automatic Windows Secure Web Patch Removal
Automatic removal of a rogue is by far the easiest and safest way to get rid of the system’s infection. A rogue deleted in this way will not be revived, because all its components are removed by antispyware. The antispyware tool decontaminates the infection and does not allow other threats to get into the system. If you want to remove Windows Secure Web easily, activate the rogue with this key 0W000-000B0-00T00-E0020 which restores Internet connection.
1) As the activation of the rogue restores the Internet, download a reliable antispyware tool. Note that you have to be sure that the antispyware you want to download is legitimate and powerful enough to delete the infection. Therefore, download a removal tool and launch it to run the scan.
2) If you do not want to download a removal tool on the infected computer, download it on a spare one. Take a removable drive and after copying and pasting the installation package onto your removable drive, transfer the antispyware on the infected computer.
100% FREE spyware scan and
tested removal of Windows Secure Web Patch*
Manual Windows Secure Web Patch Removal
This way of removal is recommended for only experienced troubleshooters, because the process of removal is a cumbersome operation, which has to be carried out very thoroughly. An average Windows user, which knows only the basics of the computer, might damage the system severely while attempting to remove the rogue manually; therefore, if you have no idea of how the removal should be do, remove the infection automatically. However, as you are the only person who knows what is best for your system, we provided you with the steps of removal.
1) Stop these rogue-related processes:
Protector[random].exe2) Open Registry Editor (enter “regedit” into the field “Run” and press “OK”) and delete the registry entries which are created by the rogue:
3) The removal is done as soon as you delete these files:





0 Comments.