What is Windows Premium Shield?
Windows Premium Shield is a fictitious anti-spyware application which uses a tremendously misleading interface. Some computer users facing the threat immediately link the represented computer scanner with the Windows operating system because of the misguiding name and the attached logo. Unfortunately, this is just a trick to fool you into trusting a completely fictitious malware remover which will not delete real computer threats. Since the threat can modify the Windows shell, you will discover that access to the desktop is disabled, and all you can interact with is the rogue anti-spyware itself. What is more, you may find that keyboard shortcuts do not help you access any Windows utilities. This is due to the fact that the malign infection can block the running of executable files. Anti-Spyware-101.com researchers recommend that you delete Windows Premium Shield if it has taken over your personal computer as well.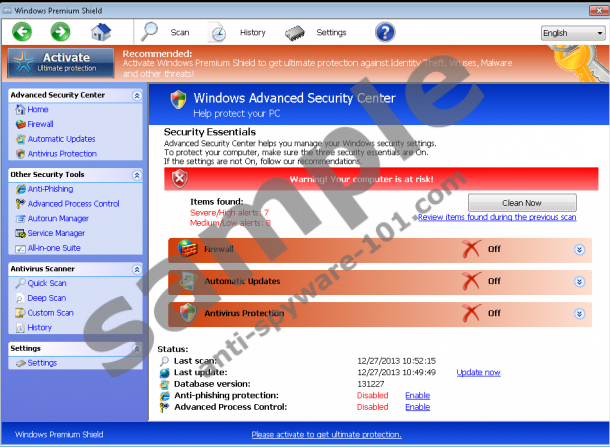


How does Windows Premium Shield work?
Even though the mischievous Windows Premium Shield uses the interface of such infamous rogues as Windows Prime Booster and Windows Accelerator Pro, it has been discovered that this threat works in a slightly different manner. It manages to dim the desktop and present the rogue’s interface, so that your full attention would be focused on the fictitious scanner rushing you to delete allegedly attacking threats. In reality, such infections as Trojan-ArcBomb, AdWare.Win32.BHO or IM-Flooder are nor running on the PC. The main reason why they are listed by the scanner is to scare you into thinking that soon enough your data will be removed or stolen or that your computer will be damaged irretrievably.
Do you think that you can restore access to the computer only if you pay the Windows Premium Shield subscription fee which may span from $49.95 to $139.90? Well, this is not the case. In fact, if you pay for the allegedly full version of the fake malware remover, your computer will not gain the protection it needs and your personal data collected during the purchase will become vulnerable. If you have already made the payment, we urge you to contact the bank immediately, so that your financial protection would be ensured. Overall, whether you have already paid the requested fees or not, the infection is still running on your computer. Continue reading to learn more about Windows Premium Shield removal.
Automatic Windows Premium Shield Removal
If you have never dealt with malicious computer infections in the past, you need to be extremely careful with the threat. Unfortunately, other dangerous threats could have been installed without your knowledge already. Therefore, we recommend using automatic malware detection and removal software to delete all running infections. Firstly, activate one of the license keys presented below to trick the rogue into treating you as a registered user. This should disable all existing symptoms and help you install authentic malware detection and removal software. We recommend SpyHunter, and you can click the download button below to install it onto your PC.
100% FREE spyware scan andtested removal of Windows Premium Shield*
License keys:
0W000-000B0-00T00-E0001
0W000-000B0-00T00-E0002
0W000-000B0-00T00-E0003
Manual Windows Premium Shield Removal
The manual rogue’s removal is the task which is extremely complicated, even if you are experienced and you know how the rogue works or how to discover other potentially existing malware. If you believe you can remove the infection manually and ensure the protection of the PC, follow the steps below.
Open the Task Manager (Ctrl+Alt+Delete) and end these processes:random.exe
Open the Registry Editor (enter regedit into RUN/Search) and remove these entries:
Locate and delete all of the files related to the malicious rogue:





0 Comments.