What is Windows Antivirus Patrol?
Windows Antivirus Patrol is a fraudulent computer application which looks like a computer security tool. The bogus program is likely to be installed without your permission; hence, the computer should contain a reputable malware prevention tool. Windows Antivirus Patrol is part of the Rogue.VirusDoctor family, which includes Windows Security Master, Windows Protection Booster, Windows AntiVirus Booster, and a great many other threats. All these malicious programs can be installed onto your computer in different ways, including file sharing websites and websites for adults. Once installed, the application launches its fake scanner, which provides you with a list of Trojans, worms, and other threats. 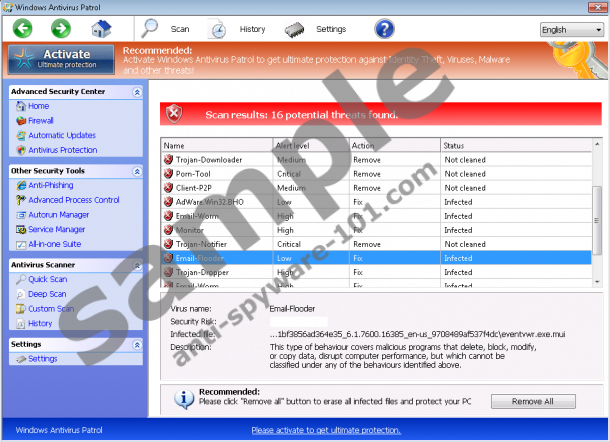
 100% FREE spyware scan and
100% FREE spyware scan and
tested removal of Windows Antivirus Patrol*
In theory, you are supposed to register the application in order to remove all those infections from the PC. The truth is that Windows Antivirus Patrol only imitates system scans; thus, those threats on the lists are not present on your PC. The rogue anti-virus program should be replaced with a legitimate and reputable one because the program in question cannot provide the system with protected against malware and spyware programs.
What else does Windows Antivirus Patrol do?
The major objection of Windows Antivirus Patrol is to make you activate it. In order to encourage you to fill in the purchase form, the rogue anti-spyware program can restrict your access to the Internet and disable executable files, which means that you can hardly use the machine. The restrictions are introduced to prevent you from removing Windows Antivirus Patrol; however, you may also think that the computer has become inoperable due to the presence of the different infections detected.
If you really want to protect your data stored on the PC and browse the Internet safely, you should rely on a legitimate security tool. Windows Antivirus Patrol may soon be replaced by another identical rogue application, which may bypass in-built system security programs and inflict new damage to the system. The sooner you take action to remove Windows Antivirus Patrol and shield the system from other computer threats, the sooner you can minimize the risk of computer infections.
How to remove Windows Antivirus Patrol?
Even though it is inadvisable to invest in Windows Antivirus Patrol, you can register the application with one of keys given below:
0W000-000B0-00T00-E0022
0W000-000B0-00T00-E0021
After activating the program, you will regain access to the Internet. Our advice is that you implement SpyHunter. This application can remove Windows Antivirus Patrol and protect the system against multiple computer threats, including other rogue anti-spyware programs, browser hijackers, Trojans, and other threats.
Remove Windows Antivirus Patrol
- Restart the computer.
- Start tapping the F8 key once the BIOS screen loads.
- Select Safe Mode with Command Prompt.
- Press Enter.
- Type cd.. next to C:\Windows\system32\ and tap Enter.
- When the line C:\Windows appears, type explorer.exe and press Enter.
- Open the Start menu.
- Click RUN or click on the Search box and
- Type %appdata%. Press Enter.
- Delete svc-[random file name].exe.
- Restart the computer.
- Open the Start menu.
- Repeat step 8.
- Type regedit and click OK.
- Go to HKEY_CURRECT_USER\Software\Microsoft\Windows NT\Current Version\Winlogon.
- Right-click the Shell and select Modify.
- Enter %WinDir%\Explorer.exe to change Value and click OK.
- Now launch a browser and go to http://www.anti-spyware-101.com/download-sph to do download SpyHunter.
- Install the application and remove Windows Antivirus Patrol.
Windows Antivirus Patrol is a complex program. It creates its files and registry entries, all of which should be eliminate from the PC. Even though we recommend using a spyware removal tool, below you will find the components of the application. Bear in mind that you remove the application at your own risk and we do not take responsibility for the consequences that follow your attempts to get rid of the infection.
1) Open the Task Manager and stop these processes:
random>.exe2) Remove these files:
3) Delete the following registry entries:





0 Comments.