What is Windows AntiBreach Tool?
Windows AntiBreach Tool is a rogue antispyware application. It is a dangerous computer infection that virtually paralyzes your system with intention to steal your money. All rogue antispyware applications have been created to fool innocent computer users into thinking that their systems are seriously infected with malware. If you see a new window pop-up that reads Windows AntiBreach Tool and there is a system scan carried out, then you have surely been infected with rogue antispyware. To protect your computer and your financial security it is in your best interest to remove Windows AntiBreach Tool from your computer as soon as possible.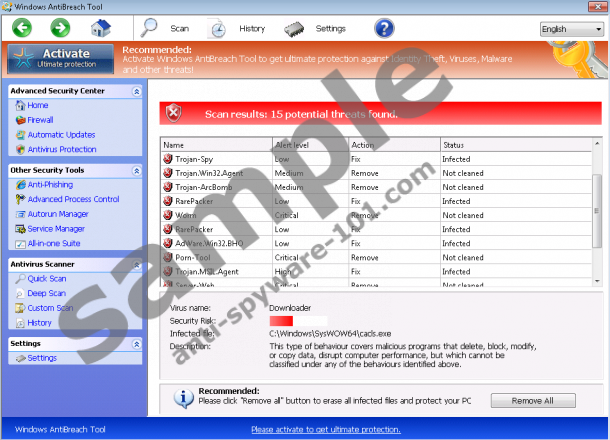 100% FREE spyware scan and
100% FREE spyware scan and
tested removal of Windows AntiBreach Tool*
Where does Windows AntiBreach Tool come from?
In reality, there is nothing new or shocking about Windows AntiBreach Tool, because the fake antivirus program is a new clone of Windows Efficiency Master. It is also practically identical to Windows Antivirus Master, Windows Ultimate Booster and other similar applications from Rogue.FakeVimes family of computer infections. The established associations give us clues on how we can deal with the rogue, but naturally, avoiding the infection should be your utmost priority.
In order to avoid Windows AntiBreach Tool, you should stay away from unfamiliar websites and do not click commercial links and other flash advertisements. Any stray click may accidentally initiate Windows AntiBreach Tool’s installation. What is more, if you receive spam emails from unknown senders do not open them. Spam email attachments are commonly used for malware distribution, so you should avoid them at all costs.
What does Windows AntiBreach Tool do?
This fake antivirus program exhibits all the main infection symptoms of any other rogue antispyware application. It also employs the same tactics as other programs from FakeVimes group. When the infection takes place, first and foremost, Windows AntiBreach Tool runs a fake system scan. It then presents you with a list of supposed computer infections such as Trojan-ArcBomb, AdWare.Win32.BHO, Trojan.MSIL.Agent and others. The fake list is generated in order to convince you that your computer is seriously infected with malware.
To make the impression more believable, Windows AntiBreach Tool blocks certain system tools that would generally allow you to remove malware. The rogue denies access to all .exe files thus successfully stopping you from accessing the Internet. It also blocks Windows Explorer virtually leaving you unable to operate your computer. It makes an impression that everything will go back to normal if you pay $79.95 for a lifetime subscription, but this is merely a scam devised to swindle you out of your money.
How to remove Windows AntiBreach Tool?
It is obvious that you cannot suffer Windows AntiBreach Tool any longer. To terminate the rogue you should acquire a licensed antimalware tool that will help you remove it automatically. Manual removal is not recommended unless you are a computer security expert. To acquire a computer security tool you need to bypass the rogue’s defenses first.
The first way to do that is to make use of one of the activation keys below:
- 0W000-000B0-00T00-E0001
- 0W000-000B0-00T00-E0002
- 0W000-000B0-00T00-E0003
- 0W000-000B0-00T00-E0011
- 0W000-000B0-00T00-E0022
- 0W000-000B0-00T00-E0023
- 0W000-000B0-00T00-E0031
- 0W000-000B0-00T00-E0032
- 0W000-000B0-00T00-E0033
Activating the rogue will make it “think” that you have acquired the full version of the program and all of the infection symptoms will disappear for a time being. While the rogue is dormant, you need to acquire a powerful computer security application and terminate it for good. In order to remove Windows AntiBreach Tool without the use of activation keys, you can follow the manual removal instructions below.
Terminate Windows AntiBreach Tool
- Reboot the PC and tap repeatedly F8 key once BIOS screen disappears.
- Select Safe Mode with Command Prompt and press Enter.
- Type cd.. next to the C:\Windows\system32 line in Command Prompt and press Enter.
- Another line appears. Type \explorer.exe in it and press Enter.
- When Windows Explorer loads, open Start menu.
- Enter %appdata% into the search box and press Enter. For Windows XP, launch Run, enter %appdata% and click OK.
- Delete the svc-[4random characters].exe file from the directory.
- Restart your computer.
- Open Start menu.
- Enter regedit into the Search box and press Enter. For Windows XP, launch Run, enter regedit and click OK.
- Navigate to HKEY_CURRENT_USER\Software\Microsoft\Windows NT\Current Version\Winlogon.
- Right-click Shell on the right pane.
- Select Modify and type %WinDir%\Exporer.exe for Value. Click OK.
- Access http://www.anti-spyware-101.com/download-sph and install SpyHunter.
100% FREE spyware scan and
tested removal of Windows AntiBreach Tool*





0 Comments.