What is XP Internet Security 2012?
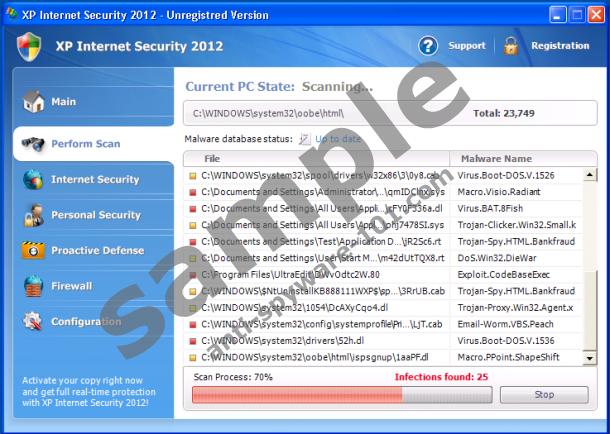
Allowing XP Internet Security 2012 to enter your computer is a bad idea, because it is a rogue antispyware application which arrives at your doorstep with one single objective only – it wants to rip you off. It has been plaguing the users around the world for some time already and now it is your turn. That is, if you do not manage to get rid of XP Internet Security 2012 in time.
This rogue can appear right in front of you even in your social network profile, in a shape of friendly personal message or random post. There you will be urged to click on the link embedded in the message, saying that it’s a funny video of you, or some really exciting picture that you simply must see. Unfortunately, the moment you click on it, you automatically initiate the download of XP Internet Security 2012.
When this rogue gets into your, it will load automatically every time you turn on your computer, sending you numerous fake security messages, saying that your computer has been terribly infected and you need to buy the full version of XP Internet Security 2012 if you want your computer back to normal. Do not do that, because then you will lose your money for good. Remove XP Internet Security 2012 for good and protect your computer from any similar threats in the future.
Were you to carry on with the removal of the rogue immediately, use these activation codes to “register” it:
2233-298080-3424
3425-814615-3990
100% FREE spyware scan and
tested removal of XP Internet Security 2012*




Automatic XP Internet Security 2012 Removal
Automatic rogue removal means that you acquire an antimalware program that deletes XP Internet Security 2012 for you. This method works perfectly well for both – amateurs and professionals, especially if you don’t want to meddle with registry and file deletion. At the same time the program you have used to remove XP Internet Security 2012 will be able to safeguard your system in the future.
However, the automatic removal might be slightly tricky, because XP Internet Security 2012 blocks all executables right after it is installed. You might “register” the rogue with one of the activation keys (233-298080-3424, 3425-814615-3990, 9443-077673-5028) and get your programs back, but that is only temporal improvement, so in order to terminate XP Internet Security 2012 for good:
- Restart your PC and then press F8 during the boot to load the Safe Mode with Networking (use arrow keys to navigate through the boot menu).
- This way you will be able to download SpyHunter onto your computer.
- Afterwards, reboot your computer again, load Normal Mode, install SpyHunter and remove XP Internet Security 2012 with it.
Or you can download SpyHunter on a completely healthy computer and then rename the installer.exe file into installer.com (so that the rogue would not block it), and transfer it into a USB flash drive. Plug the USB into the infected computer and install SpyHunter to terminate the rogue.
100% FREE spyware scan and
tested removal of XP Internet Security 2012*
Manual XP Internet Security 2012 Removal
Choose to remove XP Internet Security 2012 only if you have done something like that before. With manual removal you can get rid of the rogue completely by deleting every single file that is related to it, but it is also slightly dangerous, because you can accidentally delete system-related files and such tools like Registry Editor does not have an Undo function. Nevertheless, if you are sure that you can make it, follow these steps to erase XP Internet Security 2012 from your computer:
1) Stop and delete these processes:
2) Now open Registry Editor and delete all the following keys that has been left there by XP Internet Security 2012:
3) Find and delete the rogue-related files:





0 Comments.