What is Windows Protection Servant?
When we want to protect our computers, we should definitely stay away from threats like Windows Protection Servant. This rogue antispyware application is very good at masquerading as a real antivirus program and many users have already been fooled into spending their money for nothing by this malicious piece of software. Don’t be one of them, and delete Windows Protection Servant while there’s still time.
First and foremost, you should make sure that you don’t get this infection in your computer. That requires attention while surfing the internet. Avoid clicking on suspicious links just for the sake of clicking, because they might lead to infected sites, where the download of Windows Protection Servant is programmed to start automatically. There might be a very alluring proposal coming along with the link, but the better it sound the more suspicious it is. You might think you’re opening a webpage of your dreams, while in fact it can be just a hacked site with Windows Protection Servant as a “present” for you.
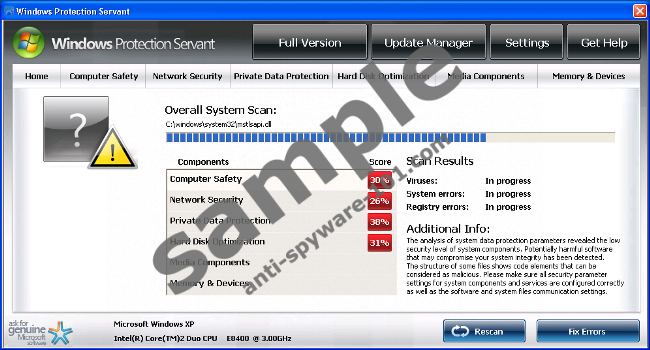
Windows Protection Servant behaves just like any other rogue out there, and it sends you various fake security messages in order to persuade you to pay for a non-existing protection. Some messages may look like this:
System Security Warning
Attempt to modify register key entries is detected. Register entries analysis is recommended.
Warning!
Location: c:\windows\system32\taskmgr.exe
Viruses: Backdoor.Win32.Rbot
Any user should ignore these messages, because they are generated only to scare users and force you into buying the program by landing you on a purchase page. Don’t provide these criminals with your credit card information, because it will result in a total loss of your money. Get yourself a reliable malware scanner and remove Windows Protection Servant from your system together with all of its components.
100% FREE spyware scan andtested removal of Windows Protection Servant*





0 Comments.