What is Windows Processes Accelerator?
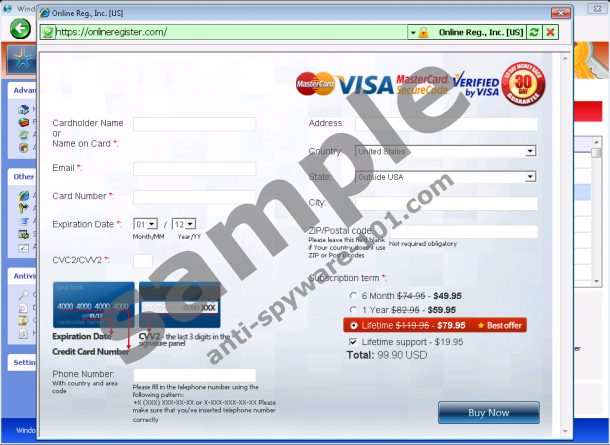
Windows Processes Accelerator is a bogus application which is trying to fool you and to leave you without money. Windows Processes Accelerator was made by cyber crooks that seek to gather your financial data and money. This fraudulent application threatens you with fake information displayed in the screen and expects that you will pay for removal of false threats. Do not believe that there is something real about this malware.
Windows Processes Accelerator pretends to run as a real security application and to sound as convincing as possible. The threats such as Trojans, malware or viruses are imaginary and do not exist in your system although presented in false messages. The scans that you get one after another do not reflect reality and real situation - they are simulated and you should never think that they are existent. The only infection is Windows Processes Accelerator which should be removed from the system.
Once you decide to remove Windows Processes Accelerator, think carefully whether you are going get rid of it manually or automatically. Manual removal of the malware is a cumbersome procedure and it should be carried on by an experienced troubleshoot specialist who would delete all the components of the rogue. An easier way to removing Windows Processes Accelerator is to find a legitimate antispyware program which would automatically detect the infection and delete it from the computer.
Warning, this parasite will block your Internet connection. Click here for instructions how to renew your Internet access.
UPDATE
It takes just one glance to realize that Windows Processes Accelerator comes from Rogue.VirusDoctor bunch of rogue antispyware applications and it is a direct clone of Windows Efficiency Reservoir, Windows Care Taker, Windows Custodian Utility and many other similar infections.
Since Windows Processes Accelerator does all it takes to achieve its goal (which includes ripping you off), it blocks your Internet access without any doubt. Without the Internet you cannot acquire the means for the automatic rogue removal. And if you are an expert it the manual removal, Windows Processes Accelerator makes sure that you are not able to perform that as well, because it blocks the access to Windows Task Manager and Registry Editor.
To make matters worse, it continuously spams you with fake security notifications:
Error
Trojan activity detected. System data security is at risk.
It is recommended to activate protection and run a full system scan.Warning! Identity theft attempt Detected
Hidden connection IP: 58.82.12.124
Target: Your passwords for sites
If you want a breather from all this, try "registering" Windows Processes Accelerator with this activation key:
0W000-000B0-00T00-E0020
Even though it does not remove Windows Processes Accelerator from your system, it cancels out the rogue's symptoms for a while and you have enough time to take care of it. If you have no idea how to do that on your own, get yourself a trustworthy antimalware program - that will detect and delete Windows Processes Accelerator along with its components. Just do not sit and wait and until the rogue comes back right at you.
100% FREE spyware scan andtested removal of Windows Processes Accelerator*










0 Comments.