What is VideoBelle Ransomware?
VideoBelle Ransomware is yet another ransomware-type computer infection based on the Hidden-Tear project. It is similar to Balbaz Ransomware, Matroska Ransomware, and Oxar Ransomware. All of them are similar, but not identical and this article is dedicated to providing you with the functionality, distribution methods and other peculiarities of VideoBelle Ransomware. Needless to say, you ought to remove this malware as soon as possible because it is set to run each time you boot up your PC, so it can potentially encrypt new files you upload to it.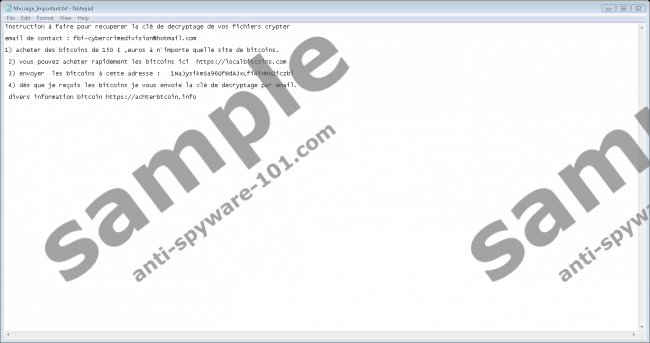
Where does VideoBelle Ransomware come from?
The Hidden-Tear project has long been abandoned by its original creator. However, other malware developers picked up where the original developer left and started developing ransomware based on the source code of Hidden-Tear. The original developer has recently apologized for making the code public because it has lead to dozens of new ransomware released that keep on being released to this day.
Like most of the ransomware based on Hidden-Tear, VideoBelle Ransomware is most likely distributed via email spam, though no concrete information has yet been found to determine the exact methods used to infect computers. In any case, if it is distributed via email, then the emails can be disguised as something they are not such as invoices or receipts and the malicious executable file attached to the emails can be disguised as a PDF document (which is often the case.) If you open or download and then open the attached ransomware file, then it will start doing its dirty work immediately.
What does VideoBelle Ransomware do?
Our cyber security experts have concluded that VideoBelle Ransomware uses the Advanced Encryption Standard (AES) to encrypt your files. It targets many file formats that include but are not limited to .txt, .doc, .docx, .xls, .index, .pdf, .zip, .rar, .css, .lnk, .xlsx, .ppt, .pptx, .odt, and .jpg. This ransomware appends the encrypted files with a “.locked” extension. However, unlike some ransomware, it does not change the file name. Testing has shown that it was configured to encrypt files in %USERPROFILE%\\Desktop, %USERPROFILE%\\Downloads, %USERPROFILE%\\Documents, %USERPROFILE%\\Pictures, %USERPROFILE%\\Music, and %USERPROFILE%\\Videos folders.
Once the encryption is complete, VideoBelle Ransomware drops a ransom note called “Message_Important” in the folders mentioned above that contains information on how to pay the ransom in the Slovakian language. The note says that you need to message the developers of this ransomware using at bi-cybercrimedivision@hotmail.com. You are required to pay 150 Pounds Sterling worth of Bitcoins. However, we advise you against doing that and recommend that you delete this ransomware instead because you cannot be certain that the criminals will keep their word and decrypt your files.
How do I remove VideoBelle Ransomware?
We hope you found this article insightful and no know what it is all about. It is a program used for cyber extortion and aims at encrypting your valuable and important files to compel you to pay a ransom for you to get them back. The problem is that you cannot trust the cyber criminals to deliver on their promise. Therefore, we recommend that you remove it using SpyHunter’s free malware scanner to detect the ransomware and delete it manually.
Removal Guide
- Visit http://www.anti-spyware-101.com/download-sph
- Download SpyHunter-Installer.exe and run it.
- Launch the program and click Scan Computer Now!
- Copy the file path of the executable from the scan results.
- Press Windows+E keys.
- Enter the file path in File Explorer’s address box and hit Enter.
- Find and right-click the executable file and then click Delete.
- Empty the Recycle Bin.
100% FREE spyware scan and
tested removal of VideoBelle Ransomware*





0 Comments.