What is Usearch.co.id?
Developers of browser hijackers such as Usearch.co.id often use appealing design and usability features to trick Internet users into believing that running such intrusive application is safe and even useful. Unfortunately, in reality, a browser hijacker is the opposite of what you would consider safe and useful. Sadly, quite a few users are tricked by these gimmicks and have this or other hijacker active on their operating system. If you are one of those users make sure not to take any chances with this hijacker as it could turn out to be a major virtual threat. It is important to understand how this malicious program works and why it should be removed. We provide our further findings about the suspicious functionally of this hijacker in this article. Along with that we have crafted a detailed removal guide that will help you terminate Usearch.co.id in just a few easy steps.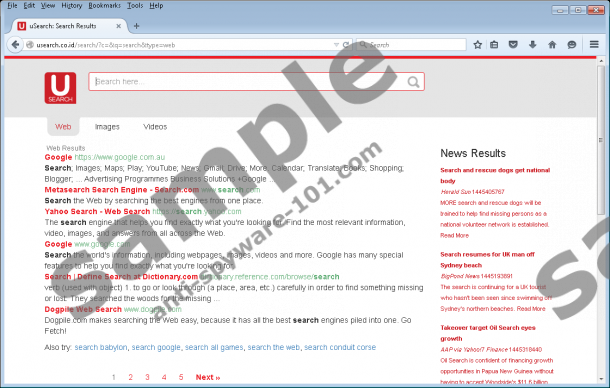

What does Usearch.co.id do?
The most common feature of a browser hijacker is its ability to alter your web browser’s default settings without any authorization; thus, the primary indication that Usearch.co.id is up and running on your PC is a change of your default search engine and homepage. These changes are made to major web browsers such as Google Chrome, Internet Explorer, and Mozilla Firefox. Such particularly wide compatibility signifies that virtually every system could be infected with this hijacker. All the changes that are made will ruin your online experience, to put it mildly. While annoyance and frustration caused by the hijacker are the most prominent features, it is important highlight the fact that the hijacker provides a suspicious search engines that should be ignored at all times. It is important to do so because at times you could expose your operating system to potentially malicious web content. This is so because some results could turn out to be implemented with redirect links. Make sure to delete Usearch.co.id as it will reduce the chances of infecting your PC with any other questionable programs.
How to improve your virtual security
There are a few simple steps that you should take and you will be able to make your operating system virtually unbreakable. Since it is widely known that in most cases suspicious software is distributed via software bundles it is quite sensible to avoid primary sources that provide such installers. In most cases these dubious software packets are obtained from third-party hosting sites; thus, downloading your software from authorized vendors’ websites will significantly reduce the risk factor of infecting your PC. It is also imperative to pay your absolute attention while conducting any installation. Often users skip a seemingly irrelevant step and end up allowing a suspicious program to be installed on their PC. If you follow the setup process carefully you might be able to cancel the installation of some unwanted third-party program. Lastly, but most importantly, you should install a professional antimalware tool without any hesitation. Such a tool provides system security at absolutely all times, meaning that you will be constantly warned by any suspicious websites or download in advance.
How to remove Usearch.co.id
The removal instructions are quite easy to follow. Just like with an installation procedure, you should not skip any steps while executing the removal procedure as it could result in a non-complete termination of Usearch.co.id. To be sure that every single bit of this hijacker was deleted entirely, you should scan your PC with a reliable malware detection and removal tool as soon as you are finished with manual removal.
How to remove Usearch.co.id from your operating system
Windows Vista and Windows 7
- Tap the Windows key on your keyboard.
- Select Control Panel and click Uninstall a program.
- Select Usearch.co.id and click Uninstall.
Windows XP
- Click Start.
- Select Control Panel.
- Click Add or Remove Programs.
- Right-click the unwanted application.
- Select Uninstall.
Windows 8
- Move the mouse pointer to the lower-left corner of your desktop.
- Right-click and then select Control Panel.
- Click Uninstall a program.
- Double-click Usearch.co.id and confirm that you want to remove it.
tested removal of Usearch.co.id*





0 Comments.