What is Taka Ransomware?
Taka Ransomware is a new malware threat that can make you feel sorry if you have not made a backup copy of your files recently on a portable drive or that you have not defended your computer with a decent anti-malware application. This ransomware can encrypt all your important files, including your documents, photos, videos, and more, which means they will be kept hostage until you transfer the ransom fee. The biggest nightmare is not even paying these criminals the wanted fee, but the experience that shows that they may not deliver the necessary private key for you to be able to recover your files. In other words, unfortunately, there is a chance that not only will you lose money but also all your files in this malicious attack. This makes this ransomware a major hit against your computer, which you should not take lightly at all. We do not think that you want to support cyber criminals to be able to go on committing online crimes, but it is, of course, understandable if you may not see any other way out of this terrible situation. Nevertheless, we suggest that you remove Taka Ransomware immediately after you notice its presence and the devastation it has done. Please read our full article to learn more about this vicious threat and how you could avoid similar malware attacks.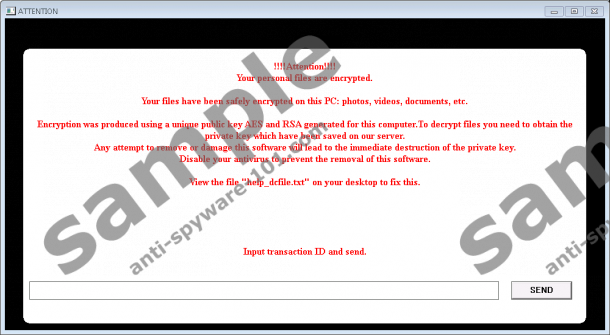

Where does Taka Ransomware come from?
The most likely way for you to get infected with this ransomware is to open a spam e-mail and view the attached file. This seems to be one of the mostly preferred methods when it comes to distributing ransomware programs. Spamming campaigns have become much trickier than they used to be and they can easily slip through your spam filter to end up in your inbox. Most users consider their inbox a safe place; therefore, they tend to open every mail they find there without a second thought. This is a mistake you may have to pay a steep price for just like in this case. Such a spam mail could seem to come from an official or legitimate source. It could pose as a legal notice, an urgent matter regarding local authorities, anything to do with your credit card details used for purchasing a product or booking a hotel room, practically anything that could matter to you or anyone really.
Even if you feel that "it must be a mistake," it is quite likely that you would still open this mail and would want to see the attached file. This attachment can pretend to be an image or text document, but it is indeed a malicious file that can drop this ransomware onto your machine and initiate it as well the moment you click to run this file. This is why you need to be much more careful around your inbox in the future because you can actually prevent such a nightmare from happening. Unfortunately, once you run this attachment, the attack will be over shortly afterwards and even deleting Taka Ransomware will not save you and your files anymore; although, this is what you are supposed to do if you ever want to use your computer again.
How does Taka Ransomware work?
Once you open the saved attachment, the main executable file, which was named "8II21E.exe" in the case of our sample, is dropped in the "%PROGRAMFILES(x86)%" folder. This file have a random name made up of 6 characters, so in your case it could be totally different. After initiation, this ransomware uses the usual AES algorithm to encrypt the targeted files and then the decryption key is further encrypted with an RSA algorithm, which makes this infection practically impossible to crack without the private key. This key is stored on a remote server and only sent to the victim if the transfer of the ransom fee can be confirmed. All your encrypted files will get a ".xxx" extension. A text file containing the ransom note and instructions is also dropped onto your desktop that is called "help_dcfile.txt." This infection also creates a scheduled task named "enc," which makes sure that this attack starts up automatically every time you log in to your Windows.
All these processes may take less than a minute, which do not give you enough time to realize what is happening or to be able to intervene and stop the encryption. When the damage is done, the ransom note image takes over your screen. This image does not actually lock your screen, so you can easily close it. This note informs you about the encryption and that you have to open "help_dcfile.txt" on your desktop for further instructions. From this text file you learn that you have to send 0.5 BTC (around 300 USD) to the provided Bitcoin address and then insert your transaction ID into the ransom note window and press the Send button. You are given 72 hours to comply with this demand; or else, you can say goodbye to your files. Although this may sound like your worst nightmare and you would like to pay right away just to get your files back, we would like to ask you to consider a number of things first, such as what if these criminals do not send you the private key or technical issues arise, and so on. We believe that the best way to protect your computer from further encryption is to remove Taka Ransomware right away.
How do I delete Taka Ransomware?
If you can move on from the sudden shock and are ready to act, we are here to offer you a manual solution to remove Taka Ransomware from your system. In fact, you simply need to delete some files and get rid of the scheduled task; that is all there is to it. Please find our instructions below this article and follow the steps carefully to make sure that you clean your system of this ugly threat. We hope that you understand now how easily you could have avoided this ransomware infection if you are more cautious about opening the malicious attached file. Whenever in doubt about a mail or its attachment, you should first double-check with the sender. Nevertheless, we believe that the best way to protect your computer is to use a professional anti-malware program, such as SpyHunter. But you can search the web for any other security tool that you find reliable and reputable enough to suit you.
Remove Taka Ransomware from Windows
- Press Win+E.
- Delete the malicious file you saved from the spam e-mail.
- Locate and delete the malicious file in the "%PROGRAMFILES(x86)%" folder. (It should have a 6 character random name and a Java icon, which may change with future variants.)
- Bin the ransom note ("help_dcfile.txt") from your desktop.
- Press Win+R and type "taskschd.msc" to start up the Task Scheduler. Hit the Enter key.
- Remove the task called "enc" from the list of scheduled tasks. (It should run the file from "Program Files (x86)".)
- Restart your computer.
tested removal of Taka Ransomware*





0 Comments.