An application known as ShinoLocker Ransomware has been introduced to the audience during a presentation at the Black Hat USA 2016 convention. This piece of software has been designed by a security researcher, pen-test tool developer and pentester Shota Shinogi mostly for further virtual security research and general education purposes. The tool can be obtained from its official website and is free of charge. It is fully customizable, and each user can build a unique version of ShinoLocker Ransomware. Even though it is a great tool to educate yourself and to have a deeper understanding of the inner structure and functionality of a basic ransomware application, our team advises to use it carefully especially if you are not and an advanced computer user since you might face some unwanted outcomes. In this report, we present the features of this malware simulator and present various ways that it could be used.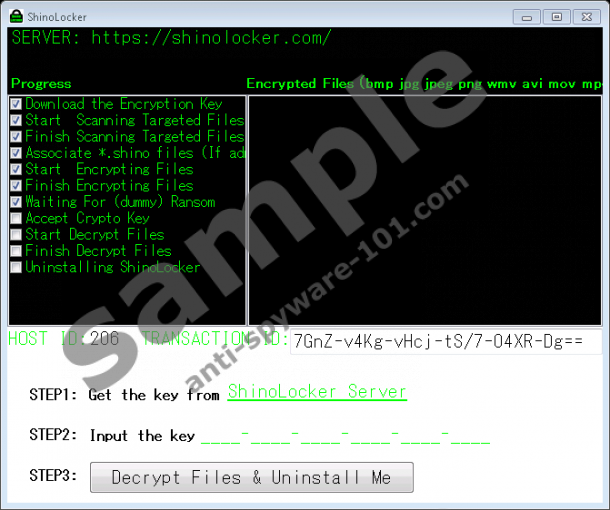


How does ShinoLocker Ransomware work
As mentioned earlier the ShinoLocker Ransomware is a customizable simulator; thus, before downloading it from its official websites, you can adjust certain functions of this tool. For instance, you can set the file types that this ransomware simulator would encrypt upon its execution. The list can be as wide as you wish or the other way around. Alongside such customization feature, you can also choose if you want to delete shadow copies and set an exact registry path of where the malware simulator would drop its value. Once you have customized this tool to your particular needs and interests, you will be able to download an executable file. Upon execution, the tool will copy its file with a random string name to the %TEMP% directory. Once this is done, and the registry entry is created the encryption procedure will start; while it takes place, you will be presented with a screen providing you with all the operations taking place step by step. As soon as ShinoLocker Ransomware completes the procedure the appointed types of files will receive a .shino extension. It is important to note that the tool uses the AES 128bit algorithm, which is a relatively weak one compared to popular ransomware programs of today since they tend to use more powerful ones such as RSA-2048 and others. All of these features that are present within this malware simulator are great as they allow you to research the malicious functionality of a ransomware program in different ways as well as it can test your forensics skills if you chose to retrieve the decryption key from the memory.
Is ShinoLocker Ransomware safe?
The educational tool in question is safe and secure for research purposes and users who hold an advanced understanding of software functionality. All the encrypted files can be decrypted as quickly as you like. This can be done by simply click the "Decrypt Files & Uninstall Me" button. Additionally, you can get a decryption key right of the official website by just typing in your host and transaction ID. There also is a great safety feature built in this software. If for some reason your files are not decrypted all of their copies are stored within the Recycle Bin; thus, you can restore the from there. It is also important to note that the only information stored within the ShinoLocker Ransomware server is the name of a computer and the name of a Windows user; if you do not feel comfortable with that, you can get this tool to work in an offline mode. Even though using it might seem not too complicated we still urge users with lesser understanding not to use ShinoLocker Ransomware as there might always be unforeseen consequences, which could prove to be rather detrimental. In such a case the creator of this malware simulator discloses that he is not liable for any loss or damage while using this piece of software.



0 Comments.