What is Search.searchrs.com?
Browser hijackers like Search.searchrs.com emerge on the web every single day. In fact, this search engine is not even a new invention but rather a clone of Search.yourinstantrecipes.com, a previous hijacker from the same creators. Although this search engine may look totally fine and innocent, you should know that engaging with the content provided by this hijacker could be risky. For example, it is possible that you download an infection bundle but you may also be taken to questionable websites where you could become the next victim of an online scam. This is why you should not take such an infection too lightly. Also, it is quite likely that you will find other malware programs on your system beside this browser hijacker. If you want to restore your system security, we advise you to remove Search.searchrs.com and all other threats you may detect on your computer. For more information, please read our full article.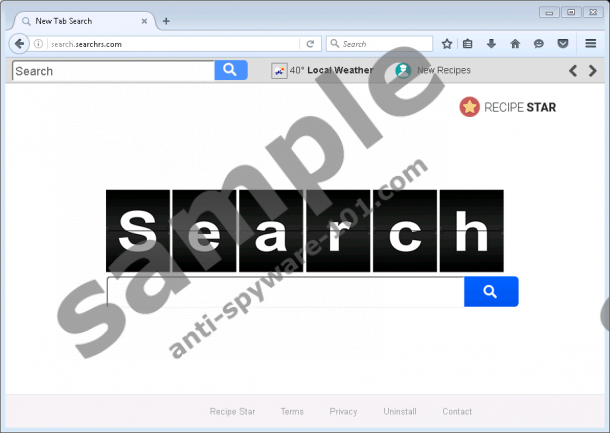
Where does Search.searchrs.com come from?
According to our malware researchers at anti-spyware-101.com, this browser hijacker is not yet popular, which, of course, does not mean that it will not start spreading widely in the very near future. The most likely way for you to let this threat onto your system is to click on corrupted third-party content. This content can possibly be a banner ad, pop-up ad, or inline link. Most often these ads are disguised so that unsuspecting computer users do not even realize that these are indeed third-party ads. This way you can encounter urgent software updates, necessary plugin download offers, Adobe Flash updaters, security warnings, and so on; of course, all of these are fake and malicious in nature. If you click on these ads, you can download a whole package of malicious threats or be taken to malicious websites where worse scenarios are possible.
There are two main possibilities for you to be exposed to such advertisements. First, your system could be infected with adware. Such an infection can display unreliable third-party ads while you are browsing the net and spy on you to trick you with customized ads. Second, you may visit questionable file-sharing websites, such as torrent and shareware pages, which are infamous for displaying unsafe third-party ads. Clicking anywhere on shady sites is risky because there could be invisible contents, too. You may simply click, for example, in a search box but this could result in a redirection to malicious sites or new browser windows may pop up with such content. We see only one solution for you if you want to save the day: You need to delete Search.searchrs.com and then, run a trustworthy malware scanner to identify all threat sources that could be still hiding on your system. You cannot be totally safe until you make sure that there is not a single potentially harmful program on board.
How does Search.searchrs.com work?
This browser hijacker is the type that displays a pseudo-toolbar at the top. This toolbar hosts a search box, which is completely redundant since there is a main search box in the middle of the page as well, and the toolbar does not show on other pages anyway. You can also find a couple of buttons leading to websites associated with recipes and cooking. Although these sites may be all legitimate and reliable, when viewing through this search engine page, you might be introduced to third-party ads coming from this hijacker. Therefore, it would not be a good idea to click on them or even visit these sites because you might cause further security-related problems.
When you run a web search through this questionable engine, your keyword is forwarded through query.searchrs.com to a possibly modified Yahoo search page. You may feel that you can trust this page since it comes from Yahoo; however, we must tell you that this browser hijacker could implant advertisements and sponsored links from its own affiliates. Since this suspicious search engine does not take any responsibilities for its third parties and the content you may be introduced to, we do not advise you to engage with anything relating to this hijacker. In fact, we suggest that you do not waste more time and remove Search.searchrs.com right away.
How can I delete Search.searchrs.com?
There are two ways for you to put an end to this threat. First, you can reset your major browsers if you do not mind that they will be set to factory default. Second, you can use our guide below as a reference to weed out whatever changes this hijacker made. Once you are done, do not forget about the other potential threats. You can try to detect them by checking your Task Manager for suspicious processes to kill, your list of installed programs for questionable applications to uninstall, or even your extension lists in your browsers if you have not reset them. You can always use our search box at the top to find descriptions of potentially harmful programs and tools. We also recommend that you keep all your drivers and programs updated so that cyber criminals cannot exploit their previous security holes.
Remove Search.searchrs.com from browsers
Google Chrome
- Tap Win+E to open File Explorer.
- In the “C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default” folder, bin the following files: Preferences, Secure Preferences, and Web Data
Mozilla Firefox
- Tap Win+E to open File Explorer.
- In the “C:\Users\user\AppData\Roaming\Mozilla\Firefox\Profiles\{Unique Mozilla user ID}” folder, open the prefs.js file (e.g., in Notepad).
- Look for the user_pref("browser.startup.homepage", "http://search.searchrs.com/") string and overwrite “search.searchrs.com” with a URL of your liking.
Internet Explorer
- Tap Win+R and type regedit. Click OK.
- Overwrite the value data (“http://search.searchrs.com”) in the following registry keys:
HKLM\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Main\Start Page (64-bit)
HKLM\SOFTWARE\Microsoft\Internet Explorer\Main\Start Page
HKCU\Software\Microsoft\Internet Explorer\Main\Start Page - Exit the registry editor.
tested removal of Search.searchrs.com*





0 Comments.