What is Search.searchfindactivec.com?
Search.searchfindactivec.com might change the homepage of your browser with your permission, but that does not make it reliable. Even if you have invited this browser hijacker yourself, you should treat it as a potential threat, and Anti-Spyware-101.com researchers recommend removing it ASAP. Why? First of all, you could reveal personal information about yourself to unknown parties when interacting with this seemingly reliable search provider. In fact, even personally-identifiable information could be recorded by this hijacker. Although this might come as a surprise to most users, the Privacy Policy statement reveals this to anyone who pays attention. Unfortunately, not many users pay attention to legal information because it is generally considered boring and incomprehensible. Well, if you reviewed the document before installing the hijacker, it is unlikely that you would have downloaded it in the first place. Needless to say, this is an important reason to delete Search.searchfindactivec.com if you have already let it in. The good news is that this infection is not hard to eliminate, and even the least experienced users should have no obstacles getting rid of it manually.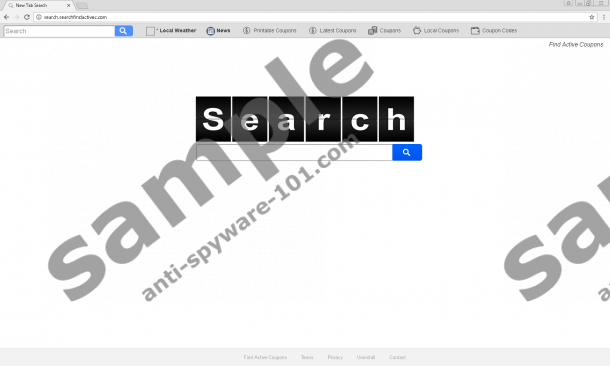
How does Search.searchfindactivec.com work?
Search.searchfindactivec.com was created by Polarity Technologies Ltd, and we have mentioned this name in many previous reports, including those analyzing Search.searchdcnow.com, Search.searchliveson.com, and other infamous hijackers. Although they are associated with different extensions and they present links to different websites, they are considered to be clones of one another. When it comes to extensions, they are introduced to users as highly useful tools, but, in reality, they are set up only to promote the hijacker. As soon as you install an extension named “Find Active Coupons” (officially presented at www.findactivecoupons.com), Search.searchfindactivec.com will replace your regular homepage, and it could also change the New Tab and default search provider. Even if you are aware of the changes before they occur, you should be curious about the functionality of the extension. If its only function is to modify your browser to introduce you to the hijacker, isn’t it kind of useless? Not only that; it is also kind of misleading because the extension itself cannot provide you with useful and reliable coupons as promised. Instead of doing that, it uses the hijacker display a few links to websites where you can find coupons.
Have you used Search.searchfindactivec.com for web browsing? This hijacker redirects all of your search queries to search.yahoo.com because it is incapable of scanning the web for useful results. The problem is that these results could include advertisements supported by the hijacker, and that makes the web search service unpredictable and potentially unreliable. If you want a reliable search provider to greet you every time you launch your web browser, you have to replace Search.searchfindactivec.com with a better option. We strongly suggest doing research before you change anything because you do not want to employ yet another unreliable and unpredictable search tool. If you do not know how to distinguish between trustworthy and untrustworthy search tools we advise checking legal information (for example, you can always find useful information in the Privacy Policy), and you should always check out third-party reviews. Of course, you can always choose one of the good old trusted search tools that are popular all over the world. That, of course, is your safest bet.
How to delete Search.searchfindactivec.com
As we have hinted previously, it is very easy to remove Search.searchfindactivec.com. We were not lying. If you change the hijacker’s URL for the homepage, the hijacker will be gone. The guides below were created for the users of Chrome, Firefox, and Internet Explorer browsers because they are most popular and because they are targeted by this specific hijacker. If you find that a different hijacker was created, and if you do not know how to change the URL on this browser, post a comment below, and we will solve this issue for you ASAP. What should you do after you modify your homepage? You should not go back to your normal activities just yet. First, install a trusty malware scanner to quickly inspect your operating system for potentially active threats. Since this hijacker is likely to come bundled with malware, you might find that you need to delete more infections. If you cannot erase them yourself, do not hesitate to employ an automated malware remover.
Removal Instructions
Internet Explorer:
- Tap keys Win+R to launch the RUN dialog box.
- Type regedit.exe to access Registry Editor.
- Move to HKCU\Software\Microsoft\Internet Explorer\Main.
- Double-click the value called Start Page.
- Overwrite the hijacker’s URL in the value data and click OK.
Mozilla Firefox:
- Tap keys Win+E to launch Windows Explorer.
- Enter %AppData%\Mozilla\Firefox\Profiles\ into the bar at the top.
- Now, move to the folder with a random name (your Firefox profile).
- Open the file called prefs.js with a preferred text reader.
- Find the hijacker’s URL, overwrite it, and save the file before closing it.
Google Chrome:
- Tap keys Win+E to launch Windows Explorer.
- Enter %LocalAppData%\Google\Chrome\User Data\ into the bar at the top.
- Move to the Default folder or the folder that represents your Chrome profile (if multiple exist).
- Open the files called Preferences, Secure Preferences, and Web Data one by one and overwrite the hijacker’s URL found in these files. Alternatively, delete them.
tested removal of Search.searchfindactivec.com*





0 Comments.