What is Search.searcheasyra.com?
Search.searcheasyra.com is a search engine owned by Polarity Technologies Ltd, a company that creates malicious search engines and browser hijackers. This particular search engine is a browser hijacker and, therefore, is also malicious because it is distributed in a malicious manner. It is bundled with installers that inject it into your browser without your knowledge or authorization. If you use it for searching the web, then it will subject you to promoted links that are included in the search results. Clearly, Search.searcheasyra.com is not the best search engine out there, but to find out just how malicious it is, we invite you to continue reading.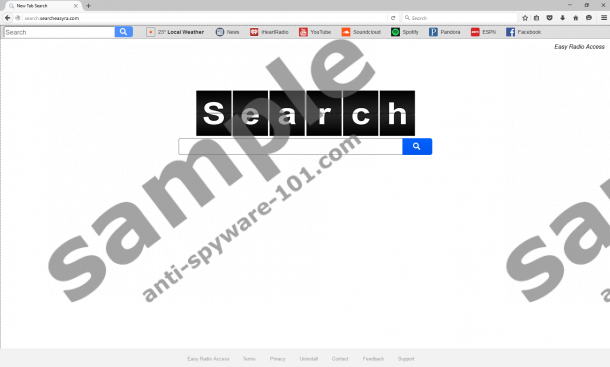
Where does Search.searcheasyra.com come from?
As mentioned in the introduction, Search.searcheasyra.com was made by Polarity Technologies, a company mainly creates browser hijackers. Apart from releasing this current browser hijacker, this company has also released Search.yourmapscenter.com, Search.youremailnow.com, Search.searchcounn.com, and many others. Evidently, Polarity Technologies is a malware developer that uses its products to promote third-party content without the user’s knowledge. Now, let us move on to how this hijacker is currently being distributed.
At the time of this article, was known to be distributed via malicious bundled software installers. Our malware researchers say that this hijacker’s developers and freeware distributers may have entered into an agreement that involves bundling Search.searcheasyra.com with freeware bundles and install into computers without the users’ knowledge or approval. You can encounter software bundles that feature this hijacker provided that you visit unreliable, fairly unpopular freeware distributing sites.
What does Search.searcheasyra.com do?
Search.searcheasyra.com functions like any legitimate search engine. However, the problem is that it redirects all of the entered search queries through a custom Yahoo search engine that will show you search results that include promoted links. These undesirable links can be of malicious nature because there is no telling who Polarity Technologies’ advertising partners are. We want to say that some links may promote malware downloads or scam or phishing websites that can jeopardize your computer’s security and your personal privacy. Researchers say that Search.searcheasyra.com is compatible with Google Chrome, Mozilla Firefox, and Microsoft Internet Explorer and it relies on freeware installers to inject it into these browsers because it does not have a browser extension.
Another thing to talk about is the fact that this browser hijacker can collect information about you and use it to show you more personalized promotional links. Researchers say that it will automatically collect information such as your IP address, Internet Service Provider (ISP) name, location, browser type, operating system type, browsing history, search queries. All of this information if on anonymous nature, but you should not allow this hijacker to obtain it because it will use it for commercial and not so legitimate purposes.
How to remove Search.searcheasyra.com
If you want to remove Search.searcheasyra.com, then all you have to do is go to your browser’s settings, erase this hijacker’s URL and enter your preferred one. Again, you should do this because this hijacker has replaced the homepage address without your knowledge and collects information about you to show personalized search results that can feature malicious links. So if you want your computer to be secure, we invite you to make use of the guide below and get rid of this browser hijacker.
Removal Guide
Google Chrome
- Press Alt+F keys.
- Select Settings.
- Click Set pages and erase this hijacker’s URL.
- Enter a URL.
- Click OK.
Microsoft Internet Explorer
- Press Alt+T keys.
- Select Internet Options.
- Erase this hijacker’s URL.
- Enter a new URL in the home page address line.
- Click OK.
Mozilla Firefox
- Press Alt+T and click Options.
- Select General.
- In the Home Page box, erase this hijacker’s URL.
- Enter a URL.
- Exit the Options menu.
tested removal of Search.searcheasyra.com*





0 Comments.