What is Savepanda@india.com Ransomware?
Savepanda@india.com Ransomware is an infection and a terrible one at that. Even if you remove it from your operating system successfully, it will leave your personal files paralyzed. This threat uses the RSA-2048 encryption key to encrypt your files, and data within them is jumbled up to make them unreadable. To decipher the files, you need a decryption key that should be created along with the encryption key. Obviously, it would make no sense for cyber criminals to share this key for nothing in return. Instead, they demand payment, a ransom, and paying it is extremely risky. As our researchers here at Anti-spyware-101.com found out, the threat is practically unbeatable, and users either say goodbye to their files or they follow the demands and pay the ransom. Well, there is one big issue with the payment, and you can read more about this in our report. We also discuss deleting Savepanda@india.com Ransomware.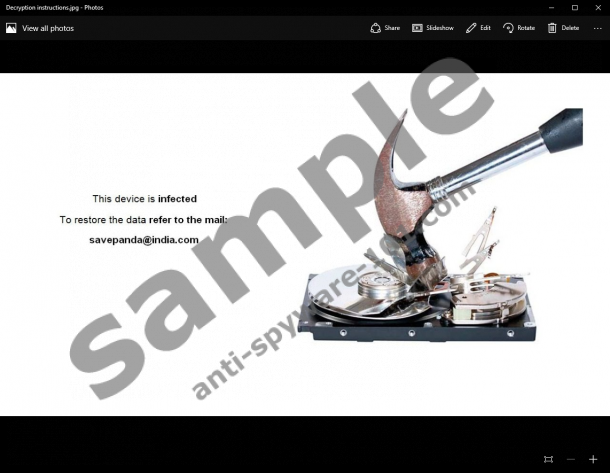

How does Savepanda@india.com Ransomware work?
Just like Cyber_baba2@aol.com Ransomware, Ninja_gaiver@aol.com Ransomware, and other infections from the same family, Savepanda@india.com Ransomware is spread in a clandestine manner. Although various different methods could be employed to distribute this threat, our researchers inform that it is most likely to hide behind seemingly harmless spam email attachments. An invoice, a document, a picture, or anything alike could be used to camouflage the launcher of the malicious ransomware. If you open it, the infection could be run automatically without you even noticing it. Once the threat is executed, it can easily encrypt all of your files. Surely, it avoids system files, but other files are not safe. Even the files of downloaded software, including .exe files, can be corrupted by this threat. You will easily identify them by the ".jpg.{savepanda@india.com}.xtbl" extension attached to them. Surprisingly, a unique ID number is not attached to this extension. This is surprising because most other threats from the family add a unique ID for the identification process. After all, if a decryption key is unique in every case, how will Savepanda@india.com Ransomware identify you? This is quite strange and disconcerting.
We are talking about decryption keys and ransom payments, but you might be completely lost if you have encountered this threat just recently and have not contacted cyber criminals yet. The "How to get data back.txt" and "Decryption instructions.jpg" files are created (one is placed on the Desktop, and the other one changes the Desktop wallpaper) to introduce you to the Savepanda@india.com email address. You are requested to email it to contact cyber criminals, and, if you do, they will inform you that you need to pay a ransom fee, and it might be quite big. Of course, paying the ransom is risky. As you now know, the malicious ransomware might have trouble identifying you, and it is possible that it does not have any intention of providing you with a key after all. What is more, even if they do have the key and can provide it to you, they might fail to do that because, after all, they care only about the money. Due to this, our researchers warn that you might lose your money if you choose to interact with cyber crooks.
How to delete Savepanda@india.com Ransomware
Obviously, you need no convincing that removing Savepanda@india.com Ransomware is important. But what should you do about your personal files? Unfortunately, paying the ransom is too risky, but there is no other way of getting the decryption key. You can try researching legitimate file decryption tools, but it is unlikely that they can save your files. We are truly hopeful that your personal files are backed up, and you can retrieve them; otherwise, you might have to say goodbye to them. In any case, removing the malicious ransomware is our priority, and we urge you to take action as soon as possible. If you have wasted all your savings on the ransom, you might have no more money to invest in automated malware removal software. In that case, you will have to approach this infection yourself, and you can use the manual removal guide below to erase the ransomware. We also recommend using a free malware scanner to inspect your PC and see if other threats still await elimination.
Removal Instructions
- Tap Win+E on the keyboard to access Explorer.
- Type the directory into the address bar (see the list of the directories you need to check below) and look for the malicious .exe file. Deleteit if found.
- %WINDIR%\System32\
- %WINDIR%\Syswow64\
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup\
- Tap Win+R keys on the keyboard to launch RUN.
- Type regedit.exe into the dialog box and click OK to access Registry Editor.
- Move to HKEY_CURRENT_USER\Control Panel\Desktop.
- Double-click Wallpaper and erase C:\Users\user\Decryption instructions.jpg.
- Go to HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers.
- Double-click BackgroundHistoryPath0 and erase C:\Users\user\Decryption instructions.jpg.
- Move to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Delete the value representing the malicious .exe file.
tested removal of Savepanda@india.com Ransomware*





0 Comments.