What is Restore@protonmail.ch Ransomware?
Security researchers have recently discovered a ransomware that has been dubbed Restore@protonmail.ch Ransomware. This particular application is designed to encrypt most of the files on your computer and demand that you pay a ransom in the form of purchasing the decryption key from its developer. It is recommended that you remove it instead because our researchers say that this program does not save the private key, so it probably impossible to decrypt the files. For more information, we kindly invite you to read this whole description.

What does Restore@protonmail.ch Ransomware do?
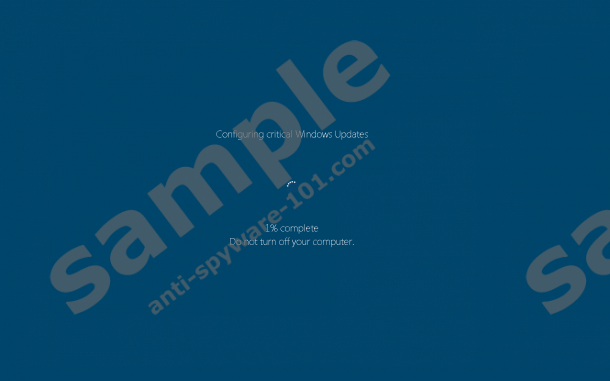
Restore@protonmail.ch Ransomware is a unique ransomware because it uses an uncommon method to divert your attention from the encryption process. If your PC becomes infected with this particular malware, then it will initiate a bogus Windows Update window that will prevent you from using your computer. While this window is up, this ransomware will encrypt most of the files on your computer. Malware researchers have yet to determine which encryption method it uses, but our security experts think that it uses the RSA cryptosystem with a 2048-bit size key. In any case, decrypting files that have been encrypted by ransomware is impossible without the proper decryption tool. So they have to have flaws that security experts can exploit to create a free to use decryption tool and share it with the world. As mentioned in the introduction, the private encryption key is not stored on the ransomware, so a decryption key might not even exist.
Research has revealed that Restore@protonmail.ch Ransomware is capable of encrypting approximately 1,300 file formats, but it will target specific locations instead of encrypting everywhere. Researchers say that it is set to target %APPDATA%, %WINDOWS%, %ProgramData%, %TEMP%, and many other locations containing important files. However, this has a whitelist of file types that it will not encrypt and they include .sys, .dll, .exe, .ico, .link, .locked, .purge, .frozen, .tmp, .temp, .dll, .ini, .manifest, .com, .prx, .bin, .am, .dlm, and .ngr. Therefore, due to the restrictions, this ransomware has limited access to some locations and does not encrypt a handful of file formats. The encrypted files are set to be appended with the .locked file extension, and after the encryption is complete Restore@protonmail.ch Ransomware is configured to place a ransom note in the form of a file named READ_ME!.hta. This file says that you need to contact the developers via the provided email address or a messaging program called Bitmsg if you do not get a reply to your email within two hours. This note also says that your unique decryption key will be deleted after a week on no action on your part. Regardless, we recommend that you do not attempt to pay the ransom.
Where does Restore@protonmail.ch Ransomware come from?
This ransomware was first spotted on the 14th of September, 2016 and our researchers say that it is a variant of Fantom Ransomware, but these two applications are not entirely identical. Still, it seems that both of them have come from the same unknown source, and it is quite possible that this developer will make more similar malicious programs in the future. Now, we want to inform you about this program’s dissemination tactics. Restore@protonmail.ch Ransomware is known to be distributed via email spam that is sent from a server set up by the developer. The emails are most likely disguised as invoices that feature a fake document (perhaps a PDF file) that drops this ransomware's main executable named stub.exe in %APPDATA%. Unsurprisingly, this application is set to infect your computer via clandestine methods, and you need to take action against it if that happens to your PC.
How do I remove Restore@protonmail.ch Ransomware?
Since there is no way of getting your files back for free, we recommend that you get rid of this ransomware from your PC either using our manual removal guide or an anti-malware application, such as SpyHunter. We want to stress that if you attempt to pay the ransom, then you run the risk of getting duped because there is no guarantee that you will get the promised decryption key.
Removal Guide
- Hold down Windows+E keys to open File Explorer.
- Enter %APPDATA% in the address line and hit Enter.
- Find stub.exe and delete it.
- Then, find and delete READ_ME!.hta
- Empty the Recycle Bin.
tested removal of Restore@protonmail.ch Ransomware*





0 Comments.