What is Play-Bar.net?
If you want to be efficient when browsing the web, Play-Bar.net is not a tool you should use. In fact, we do not recommend this search provide to anyone because it is unreliable and possibly even dangerous. Anti-Spyware-101.com malware specialists have tested this suspicious search tool, and the first thing that became obvious is that this search tool is a browser hijacker. Of course, we cannot claim that this search tool will take over browsers without permission in all cases, but it is known that this infection can act in an illegal manner. What is more, the way this program acts in the background is disconcerting as well. We suggest reading this report to learn how to remove Play-Bar.net.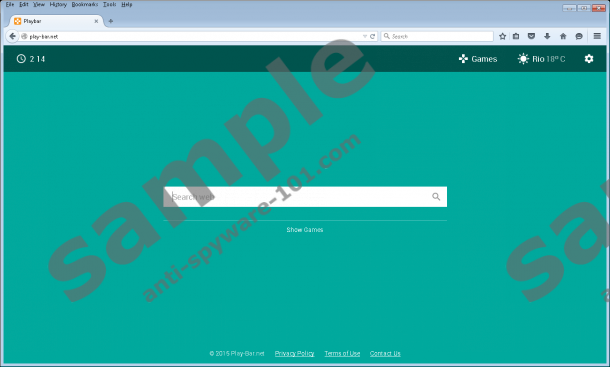
How does Play-Bar.net work?
Play-Bar.net was built by Blisburry LLP, but the distribution of this hijacker is highly questionable. Since an official installer does not exist – and it would be strange if it did – our guess is that this hijacker is distributed by third-party installers. Although this infection is considered dangerous, it could travel packaged with much more clandestine and malicious threats. Trojans, advertisement-supported programs, and even potentially unwanted programs could cause many problems, which is why you have to make sure that your operating system is clean at all times. Needless to say, the existence of Play-Bar.net reveals that your virtual security is weak, which makes your operating system the perfect target for malware distributors. If you want to learn if third-party infections have infected your PC, click the Download button below and run a full system scan.
You might have noticed already that Play-Bar.net reroutes to search.smartshopping.com, or some other suspicious search engine. Our researchers have also found that your search queries could be conducted via esurf.biz/?ssid?, which is another browser hijacker. This sort of activity is not normal, and it makes the hijacker even less reliable. All in all, whichever search engine you end up on, it is most likely that you will be exposed to advertisements instead of search results. Of course, even popular search tools show ads, but the ones represented by Play-Bar.net are extremely unpredictable, and clicking on them could bring an avalanche of security issues. If that is not enough, it was found that the hijacker can enable the data-tracking technologies that are controlled by third parties, which puts your virtual identity at risk.
How to delete Play-Bar.net
It is obvious that postponing the removal of Play-Bar.net is not a good idea. This browser hijacker deserves immediate elimination, and we have a few tips that will help you get rid of this infection. The first thing you should do is use an automated malware remover to clean your system. If you discover that your browsers are still hijacked, you can use the guide below to fix this issue. If you follow this advice, you will also initiate the removal of all other threats that cyber criminals could have infiltrated your operating system with. Keep in mind that one single malicious file can do a lot of damage, and it is awfully easy to leave these files behind if you proceed manually.
Remove Play-Bar.net
Google Chrome:
- Launch Chrome, tap Alt+F, and select Settings.
- Move to On Startup, select Open a specific page or set of pages, and hit Set pages.
- Identify the undesirable search provider, overwrite the URL, and click OK.
- Move to Appearance, select Show Home button, click Change, and repeat step 3.
- Click Manage search engines (under Search) and apply the preferred search provider.
- Identify the undesirable search provider, click X on its URL, and click Done.
Internet Explorer:
- Launch Internet Explorer, tap Alt+T, and click Manage Add-ons.
- Move to Search Providers and apply the preferred search provider.
- Select the undesirable search provider, click Remove, and click Close.
- Tap Alt+T one more time and choose Internet Options.
- Click the General tab, overwrite the Home Page URL, and click OK.
Mozilla Firefox:
- Launch Firefox, tap Alt+T, and select Options.
- Click General (in the menu on the left) and overwrite the Home Page URL.
- Move to the Search menu and Remove the undesirable search provider.
tested removal of Play-Bar.net*





0 Comments.