What is ihurricane@sigaint.org Ransomware?
Ransomware programs are extremely common nowadays so being aware of them is crucial if you wish to keep your system safe and secure. A recently discovered application of this classifications goes by the name of ihurricane@sigaint.org Ransomware. Just like its counterparts, this malware must not be taken for granted since its functionality could have devastating outcomes, to say the least. Upon intrusion it will silently and without any authorization lock your personal files. To avoid all of this and to have a fully secure system at all times, you must take preventative steps to improve your overall virtual security. In this article, we present further information regarding this intrusive application's inner workings that will make you realize why it should be removed as soon as possible. To completely delete ihurricane@sigaint.org Ransomware without encountering any major problems, make sure to use our comprehensive removal guide that we provide below.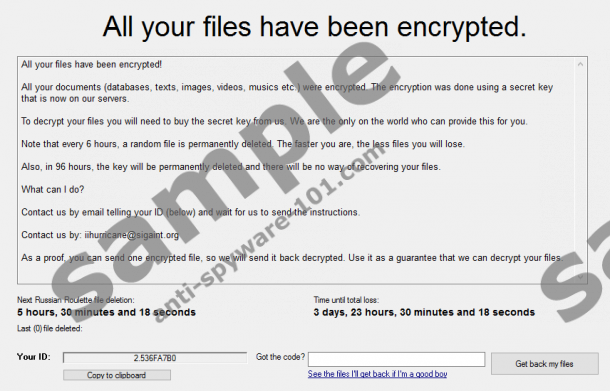
What does ihurricane@sigaint.org Ransomware do?
During the analysis, our research team has discovered that ihurricane@sigaint.org Ransomware is a newer version of another infamous malware entitled Stampado Ransomware. So it is quite natural that the two function alike. As soon as his malicious program enters your operating system, it will start doing its dirty work immediately. It is important to note that the encryption procedure triggered by it is utterly silent; this means that users without advanced computer knowledge will likely have no idea that their data is being locked away from them. Like its predecessor, the ransomware in question uses an AES-256 algorithm to encrypt your personal files; due to the strength of this cipher, a manual decryption procedure is an impossible task. All the files affected by it will receive a .locked extension. After all of this is done you will be presented with a warning message. It will inform you that your data has been encrypted and that you need to pay a ransom in 96 hours since a unique key, which is required for a decryption procedure, will be destroyed. While paying the ransom might seem like a solution to your problems, we highly recommend refraining yourself from doing so because there is no guarantee that cyber crooks who developed this malware will actually unlock your data. Thus, trusting them and making the payment could result in a huge loss of money and data. Every user that has ihurricane@sigaint.org Ransomware active on their personal computer must take immediate action to remove it.
How to improve your virtual security
Malware researchers working at our internal labs have found out that ihurricane@sigaint.org Ransomware is often distributed disguised as a useful application. This is not a new technique used by malware developers; often cyber crooks use manipulative marketing techniques to lure users into obtaining their useless and sometimes malicious programs. To significantly reduce the chances of coming across dangerous installers, make sure to avoid all third-party download sites because they are notorious for being the primary source of software bundles. Your best bet to acquire a clean installer is by downloading it from authorized vendors' websites only. We also urge you to find out as much as possible about an application that you wish to have before obtaining it; you can do so by checking the list of harmful software on our websites. By doing so, you might be able to bypass a malicious program. Finally, our researchers firmly recommend installing a professional antimalware tool as it can detect and warn you in advance about any potentially dangerous application. If you consider yourself a security conscious users, do not hesitate to take all these precautionary steps as they will allow you to maintain a fully secure operating system at all times.
How to remove ihurricane@sigaint.org Ransomware
The complete removal of ihurricane@sigaint.org Ransomware is a must. Otherwise, you risk losing a huge amounts of personal data. Do not skip any steps of the removal procedure as it could result in an incomplete removal, which might mean that traces of this malware could still be used for it to function. In other instances, those same leftovers could trigger a silent restoration procedure of ihurricane@sigaint.org Ransomware. To avoid finding yourself in such a situation, make sure to conduct a thorough analysis of your PC for traces associated with this malicious piece of software right after you have executed the manual removal. If you happen to find such analysis too complicated, we recommend scanning your personal computer with a professional antimalware tool which can detect and delete any files or registry entries linked to the ransomware in question.
How to remove ihurricane@sigaint.org Ransomware from your PC
- Click the Windows button.
- Type regedit into a search box and tap Enter on your keyboard.
- Navigate to HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run.
- Select a malicious registry value called Windows Update and then remove it.
- Open your File Explorer.
- Go to C:\Users\[your username]\AppData\Roaming.
- Select and remove a malicious files entitled scvhost.exe. In some cases this file could have a randomized name.
- Right-click the Recycle Bin and select Empty Recycle Bin.
tested removal of ihurricane@sigaint.org Ransomware*





0 Comments.