What is Extractor Ransomware?
Probably the worst that can happen in your virtual world is that a malware infection like Extractor Ransomware finds a way to penetrate it. This malicious program can slither onto your system without your noticing it and damage your files beyond recognition. In other words, this ransomware can encrypt your files with an algorithm to make them unusable for you. No wonder you cannot view or open any of your personal files, including your documents, photos, and archives. You may think that you can recover your files if you pay the ransom fee but, unfortunately, our research and our experience both indicate that there is little chance for you to get anything in return. Cyber crooks could not care less about your encrypted files and whether they remain inaccessible. We do not claim either that it never happens that your files can be decrypted after paying the demanded fee, but you should consider that you would support cybercrime this way. All in all, we advise you to remove Extractor Ransomware as soon as possible so that you can start rebuilding your system.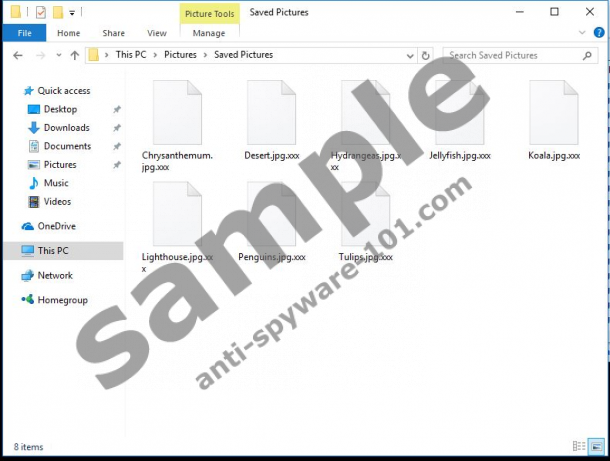

Where does Extractor Ransomware come from?
It is possible to get infected with ransomware programs in a couple of ways. For example, if you do not update your browsers and your Java and Flash drivers regularly, you could be in big trouble when landing on a malicious page created with Exploit Kits. In this case, loading the malicious page in your browser is enough for it to drop the infection behind your back. This is why it is essential that you remember to keep all your drivers and software updated. Also, you should always update using official websites because a lot of infections happen by clicking on fake pop-up updates that can also drop similar threats onto your system. We also recommend that you stay away from suspicious websites generally associated with file sharing, online gambling, gaming, and porn. These websites can expose you to unsafe third-party advertisements and misleading content, such as fake buttons and notifications. One click on such an ad or fake content and you could drop a dangerous infection onto your machine.
Although these previous examples can happen anytime at all, we cannot confirm that this ransomware uses these methods. Instead, you can find this malicious program spreading as a fake file attachment in spam e-mails. This attachment may appear to be an image, a video, or a text document, sometimes even a .zip archive. But, in reality, it is an executable file that activates this malicious attack. Cyber criminals have their methods to make you want to open this mail and download the attachment. They use simple tricks really to convince you that the mail you see in your list is indeed an important and urgent one. Please remember that you cannot restore your files after this attack even if you delete Extractor Ransomware from your system. The only possible way for you right now to recover your precious files is to have a backup copy on a removable hard drive.
How does Extractor Ransomware work?
We have no information about the encryption algorithm this ransomware uses to encrypt your files, but it is most likely the most widely used is AES-256. Since this algorithm is in fact a built-in function of your Windows operating system, the whole attack can be over within one single minute depending on the number of targeted files and your PC performance. The files that have been taken hostage get an “.xxx” extension so that you can see the extent of this attack. Do not even try to rename your affected files because it will all be in vain; it will not recover your files at all.
This ransomware does not seem to replace your desktop background or block any system processes. Instead, it places a text file named "ReadMe_XXX.txt" on your desktop and in your C:\ folder, which is the ransom note. This note uses plain language and a short message to inform you about the next step. You have to write an e-mail that includes your computer ID, which is a few-digit number in your note, and send it to "serverrecovery@mail.ru." This mail server leads us to the assumption that the creators of this ransomware might be Russians. But since the note is in English, they most likely target anyone around the world. You should know that sending money to cyber criminals rarely ends well. It is more likely that you will be infected by further serious threats disguised as a decryption tool than you could really decrypt your files. We suggest that you remove Extractor Ransomware right away if you want to start to have a secure computer.
How can I delete Extractor Ransomware?
If you are ready to act, here we are with the solution regarding the removal of Extractor Ransomware. First, you should delete the malicious .exe file you downloaded from the spam e-mail and then, all related files if you find any, including the ransom note text files. It is always worth checking the net for a free file recovery tool because malware hunters may find a way. However, if you are not an advanced user, we do not advise you to do this alone. If you see no way to recover your encrypted files, you can also bin all of them. Protecting your system with a decent anti-malware program (e.g., SpyHunter) should be your priority if you want to feel safe while using your computer. No matter how you decide though it is important that you update all your software and drivers regularly and that you stay away from suspicious websites and clicking on random third-party ads.
Remove Extractor Ransomware from Windows
- Launch your Windows File Explorer by tapping Win+E simultaneously.
- Delete the malicious file you downloaded and any other suspicious file you have recently saved.
- Bin "ReadMe_XXX.txt" from "C:\" and from your desktop.
- Empty your Recycle Bin and reboot your computer.
100% FREE spyware scan and
tested removal of Extractor Ransomware*





0 Comments.