What is Dr Jimbo Ransomware?
You should be aware of the fact that a new ransomware infection Dr Jimbo Ransomware seeking to lock files and then extort money from users has recently appeared on the web. As it is new, it is not very popular; however, it is very likely that it will become prevalent in the future, so if you do not want to find all your personal files encrypted one day, you need to take care of your system’s safety. If it is too late and you have already encountered Dr Jimbo Ransomware, you need to remove this infection from your computer. All users, except those that are going to transfer the money required by this ransomware infection, should eliminate Dr Jimbo Ransomware as soon as possible. We will share the knowledge we have about the removal of ransomware infections in the article, so you have to be very attentive while reading it.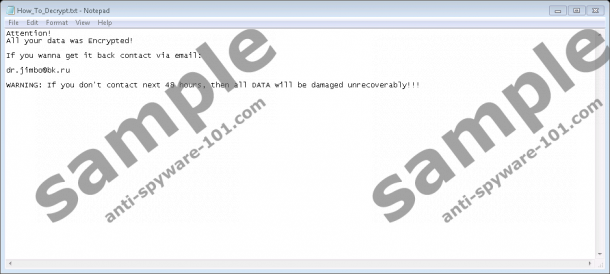
What does Dr Jimbo Ransomware do?
Dr Jimbo Ransomware enters systems with an intention of locking files and then demanding a ransom. Specialists say that this infection, most probably, uses the AES encryption algorithm, which means that it is basically impossible to get the key for the decryption of files without paying the money. Fortunately, Dr Jimbo Ransomware has no intentions of ruing the computer, so it will leave files that are located in the %WINDIR% directory (this directory contains files that belong to Windows OS) unencrypted. Even though it is not interested in system files, there is no doubt that Dr Jimbo Ransomware will encrypt all personal files, including pictures, images, videos, music, and various documents. You can be sure that the file is encrypted if it has the .encrypted extension, e.g. picture.jpg.encrypted. The encryption process starts when the ransom note (the .txt file) is opened. Dr Jimbo Ransomware needs only several minutes to encrypt the entire computer.
Once the threat finishes encrypting files, it puts the ransom note in all the folders containing encrypted files. The ransomware infection will create one ransom note for one encrypted file, which means that some folders might contain a bunch of .txt files. In addition, it seems that the name of the .txt file might be based on the name of the encrypted file, for example, picture.jpg.How_To_Decrypt.txt. Fortunately, this threat will not make any other changes, e.g. it will not lock your Desktop or change the background picture. Of course, it does not mean that it becomes less dangerous because of that.
The ransom note Dr Jimbo Ransomware creates does not contain much information. Users are simply told to contact the person who is responsible for the presence of this threat on your PC by the provided email address within 24 hours:
Attention!
All your data was Encrypted!
If you wanna get it back contact via email:
dr.jimbo@bk.ru
WARNING: If you don’t contact next 24 hours, then all DATA will be damaged unrecoverably!!!
Even though the cyber criminal that hides behind Dr Jimbo Ransomware tries to scare users into writing an email immediately, we do not think that you should do that if you are not going to pay money. Yes, we are sure that you will be asked to do that. Do not worry; users who decide not to do anything can try to recover files from a backup they have. Also, there is no doubt that the free decryptor will be released in the future, so they can wait for it instead of making a payment. To be honest, it is quite risky to pay the ransom this threat demands because you might pay money but do not get the decryption key.
From the more technical perspective, Dr Jimbo Ransomware does not make copies of itself and works at the point of execution, which means that it will not be very hard to delete it. Of course, you will still notice several modifications, for instance, the main ransom note will be put in the %HOMEDRIVE% directory and the value Happy Letter will be created in HKCU\Software\Microsoft\Windows\CurrentVersion\Run to make it possible for the ransomware to open the ransom note file automatically.
How to delete Dr Jimbo Ransomware
Below the article specialists at anti-spyware-101.com have placed the manual removal instructions that should help you to delete Dr Jimbo Ransomware from the system easily and quickly. Unfortunately, this does not mean that your files will be unlocked; however, at least, this ransomware infection will not encrypt your new files again. In most cases, systems also contain other infections that might download other malicious applications on the computer and thus cause harm to the system. Therefore, we highly recommend scanning the system with an antimalware scanner like SpyHunter to make the system perfectly clean within seconds. The diagnostic version of this scanner can be downloaded from our website – click on the Download button. Make sure you do that after you erase Dr Jimbo Ransomware fully.
Remove Dr Jimbo Ransomware manually
- Locate the malicious file you have downloaded and opened.
- Delete it.
- Tap Win+E simultaneously.
- Enter %HOMEDRIVE% into the address bar and tap Enter.
- Locate the ransom note (the .txt file) and remove it.
- Close the Windows Explorer and launch RUN (Win+R).
- Enter regedit.exe into the box and tap Enter.
- Move to HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
- Right-click on the Happy Letter value and select Delete.
- Eliminate ransom notes from different folders.
- Empty the Recycle bin and restart your computer.
tested removal of Dr Jimbo Ransomware*





0 Comments.