What is CryptoViki Ransomware?
A black desktop wallpaper and a warning saying that all your disks are encrypted are the features of the CryptoViki ransomware. The infection encrypts numerous files and demands for a ransom. After making the data inaccessible, the CryptoViki ransomware deletes itself, but that does not solve your problems. Some files associated with the infection still remain on the computer, so it is important to terminate them too. It is also worth paying more attention to the system security to prevent similar incidents in the future as your data may get stolen one day.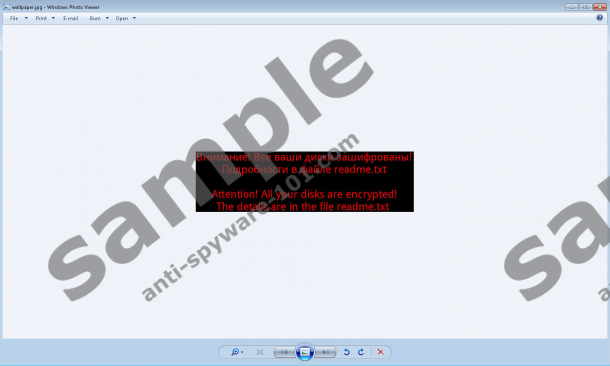


How does the CryptoViki ransomware work?
The CryptoViki infection is powered to encrypt data using both AES and RSA encryption methods, which are commonly encountered in ransomware. The infection also alters file extensions. More specifically, it adds its .viki extension. For example, the file Jellyfish.jpg is changed to Jellyfish.jpg.viki. As for the encryption methods, the two methods are different in the way the data can be encrypted and decrypted. The AES method works with the same cryptographic keys for encryption and decryption as opposed to the RSA method, where the public and private keys are used for data coding. In case of the two encryption methods, ransomware infections encrypt the victim's files and leave a decryption key which is again encrypted using another encryption method. Usually cyber criminals are not capable of providing the victim with a decryption key in return to the release fee, so our team at Anti-Spyware-101.com advises you against interacting with attackers so as not to experience money-related consequences. Typically hackers think out victims' abilities to pay the release fee; nevertheless, the costs imposed are usually rather high, but the statistics show that ransomware schemers' profits are increasing.
What does the ransomware demand for?
Interestingly, all the information concerning the data lock-up and the ransom is displayed in a .txt file. Some time ago, full-screen notifications were very popular among cyber criminals. Recent detections show a new tendency to display all the necessary information in .txt files. According to the ransom warning of the CryptoViki, the victim has to contact someone behind this infection at cryptoviki@gmail.com to get more information. The odds are that the victim would be asked to buy bitcoins and send them to a certain digital wallet. The CryptoViki ransomware is an instance when the release fee is not specified in the warning, which is becoming a new tendency.
As for bitcoins, this currency is a digital currency that is not owned or managed by any bank. Money transactions are made anonymously to so-called digital wallets. The currency is generated by "mining" bitcoins, which is done by using the resources of registered users' PCs. As there is no central issuer of this currency, it is barely possible to track money transactions, so the attackers behind ransomware remain unidentified and are getting richer every month. Because of the criminals' abilities to produce malicious programs that corrupt tens and hundreds of files, PC users should take action prevent cyber attackers.
Ransomware is a dangerous threat for individuals and businesses alike, and its overall aim is to stop you from accessing data that is valuable to you. Hence, it is crucial to shield your computer from various threats, including data stealing Trojan horses, browser hijackers, spyware, and many other types of malware.
How to remove the CryptoViki ransomware?
The CryptoViki ransomware deletes itself after encoding your files, but some malicious files may still be present on the PC. You can try finding them with the help of our removal guide. You remove those files at your own responsibility since we cannot pinpoint the specific files related to the infection because every time they vary. If you want to have the system scanned and the malicious files identified by a professional malware and spyware prevention program, use our recommended program. If your desktop background is changed to a black screen with a warning written in Russian and English claiming that your data is encrypted, it is high time you took care of your operating system, so act right now.
Remove CryptoViki Ransomware
- Delete the files wallpaper.jpeg and readme.txt.
- Check your download locations for malicious files and delete them.
- Empty the Recycle bin.
100% FREE spyware scan and
tested removal of CryptoViki Ransomware*





0 Comments.