What is Brickr Ransomware?
You might be responsible for letting Brickr Ransomware in if you executed this infection yourself by accidentally opening a corrupted spam email attachment. This is how this infection spreads. Soon after execution, the malicious file initiates the encryption of personal files to keep them hostage when demanding a ransom from you. While your files are being encrypted, a decryption key should be created as well, and this is what the creator of the ransomware will offer you in return for the ransom. Though the transaction might seem real, it is very possible that you would not see a decryptor after you transferred the ransom to the appropriate Bitcoin Address. You are introduced to the ransom and provided with instructions on how to pay it via the message that can be shown to you in two different ways. Hopefully, you can get your files decrypted, but even if that fails, you need to delete Brickr Ransomware, and the sooner you do it, of course, the better.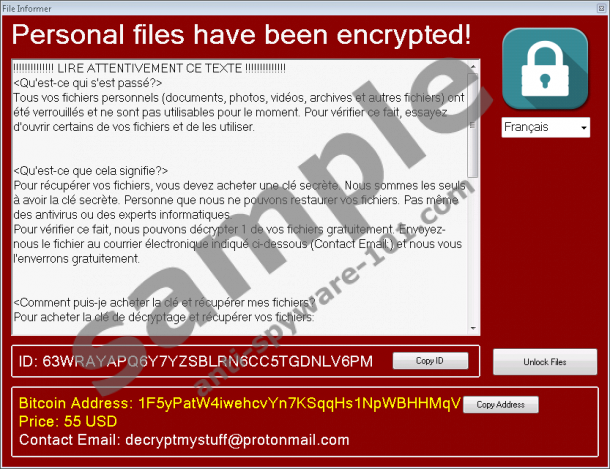

How does Brickr Ransomware work?
The notification that the malicious Brickr Ransomware uses to introduce you to the ransom is represented via a window called “File Informer,” as well as via a .txt file called “READ_DECRYPT_FILES.txt”. The window pops up automatically as soon as the encryption of your files is complete, and the TXT file can be found on the Desktop. It is safe to interact with both the file and the pop-up, and what you need to be more concerned about are the instructions that you are provided with. If you follow them, you will transfer a ransom of 55 USD in Bitcoins to 1F5yPatW4iwehcvYn7KSqqHs1NpWBHHMqV, which is a Bitcoin Address set up by the creator of Brickr Ransomware. Afterward, you will email the creator your ID number to decryptmystuff@protonmail.com. The ID number can be found in the ransom note, but it is also stored in the “id.bin” file located in %APPDATA%. Allegedly, this is what you need to do to get your files decrypted, but our analysts at Anti-Spyware-101.com warn that this could be false information. You could end up paying the ransom for no good reason, and although $55 is not a lot, you do not want wasting it.
All kinds of files can be encrypted by the malicious Brickr Ransomware, but it appears that this infection only targets those files that are in specific directories. Here is the list:
- %ALLUSERSPROFILE%\Microsoft
- %PUBLIC%\Music
- %PUBLIC%\Pictures
- %USERPROFILE%\Desktop
- %USERPROFILE%\Documents
- %WINDIR%
Obviously, this infection is most likely to affect personal files because you might be unable to recover them. Hopefully, you have these files backed up, and you can transfer them back onto your PC in place of the encrypted files as soon as you remove Brickr Ransomware. Do not log into cloud storage or hook up external drives while this malicious infection is still active. If backups do not exist, there is nothing you can do because legitimate file decryptors cannot help you. Should you pay the ransom? As it was mentioned already, paying it is very risky because you do not know what cyber criminals will do. Ultimately, it is your choice, and you have to do whatever feels right for you.
How to delete Brickr Ransomware
If you have absolutely no experience eliminating malware, removing Brickr Ransomware can be quite difficult for you. Essentially, you only need to kill a malicious process, find and delete a malicious file, and modify the Registry. All of these steps are shown in the instructions below. If you lack experience, you should install legitimate anti-malware software, and this is something we recommend even if you are experienced and if you manage to delete the ransomware manually. Why? The answer is simple: Because it can ensure full-time protection. If you do not use tools that could protect you while you browse the web, download software, or open spam email attachments, malicious infections could slither in without any warning. Needless to say, there are plenty of dangerous threats that are just as malicious as or more malicious than Brickr Ransomware, and we are sure you want to protect your operating system against them.
Removal Instructions
- Simultaneously tap Ctrl+Shift+Esc to launch Task Manager.
- Click the Processes tab and identify the unwanted process with a random name.
- Right-click this process and select Open File Location to access the malicious launcher (the location might be %TEMP%, %USERPROFILE\Desktop, or %USERPROFILE\Downloads).
- Go back to the Task Manager, select the malicious process, and click End Task.
- Move to the folder representing the malicious launcher, then right-click it, and select Delete.
- Simultaneously tap Win+R to launch RUN.
- Type regedit.exe and click OK to access the Registry Editor.
- Using the pane on the left, move to HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run.
- Right-click and Delete the values called WidnowsNetworkingSvc and WidnowsNetworkingSvcn.
- Empty Recycle Bin and then immediately perform a full system scan.
100% FREE spyware scan and
tested removal of Brickr Ransomware*





0 Comments.