What is AutoEncryptor Ransomware?
AutoEncryptor Ransomware is a malicious computer infection whose ultimate goal is to obtain your money. Ransomware infections are created massively with the aim of making victims pay large sums of money, which vary approximately from 100 to 500 US dollars. The latest ransomware infections provide requirements to use the digital currency Bitcoins, which enables attackers' anonymity. In the case of AutoEncryptor Ransomware, the attackers seem to be unaware of the value of 1 bitcoin as they demand a 10.000 bitcoins release fee. This amount of money is more than 10 million US dollars. In general, a lot of unsuspecting computer users get trapped by ransomware and pay the money required, but the victims affected by the AutoEncryptor Ransomware are likely not able to afford their data recovery. All that you can do with the AutoEncryptor infection is remove it from the PC and take action to prevent similar future incidents.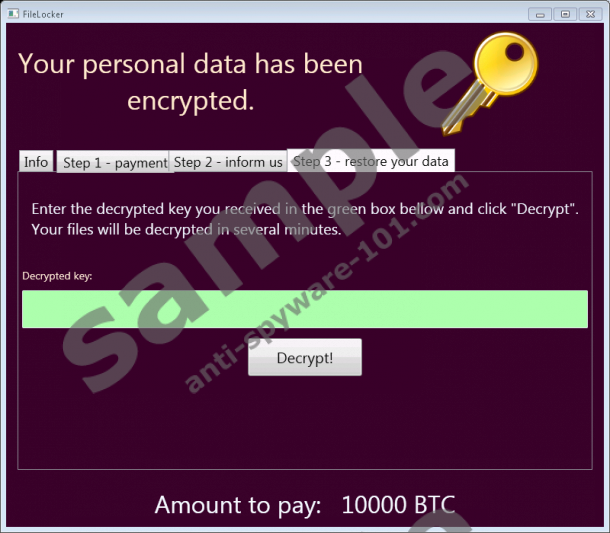


How does the AutoEncryptor Ransomware work?
First, it is worth mentioning that the AutoEncryptor Ransomware is not a finished product. Written in the .Net framework, it misses several functionalities. For example, unlike the vast majority of ransomware infections, the AutoEncryptor Ransomware does not lock the screen. In many other ransomware cases, the screen is locked, and no folder can be opened. Another interesting feature of the ransomware is its incapability to connect to a remote server. Even thought the ransomware does not communicate with the attackers, it does inflict harm on the computer.
The AutoEncryptor Ransomware uses double encryption, including AES-256 and RSA-2048. The first encryption method is used to encrypt different file types, such as .jpg, .exe, .txt, .zip, and many others. As you can tell, the ransomware infection search for most popular files. The encrypted files are marked by appending a new file extension .ENCR, which follows the original extension. The encryption key utilized for compromising your data is then also encrypted with the RSA-2048 key.
The analysis has revealed that the AutoEncryptor Ransomware encrypts files in several locations. In Windows XP, the infection searchers for files in the %USERPROFILE% directory. More specifically, it currupts files in the My Documents folder, My Pictures folder, and Desktop folder. In case of Windows Vista and newer versions, the ransomware encrypts files stored in the My Pictures, Desktop, Documents, and Pictures folders. Although the infection does not remove the files, it does make them worthless as you can no longer use them them as usual. Additionally, the infection drops its malicious files in the Documents folder and on the desktop and also sets itself up to start running once you log on to the system.
According to the ransomware warning, which is displayed in a window named FileLocker, the victim has to purchase the required sum of bitcoins from simplecoin.cz and send the attackers the encryption key given in the third tab of the window of the infection. The email address, babis@mfrc.cz, provided to the victims is invalid. Moreover, it refers to a famous political and business figure in Czech Republic. As the URL address given by the ransomware suggests, the infection is targeted at computer users based in Czech Republic. Moreover, the email address has also been chosen on purpose, that is to confuse victims as much as possible. The truth is that ransomware is created in order to defraud inexperienced computer users, so there is no need to waste money for decryption. The AutoEncryptor Ransomware is an instance of a cyber attack, and there is no guarantee that the cyber gang behind this threat is willing to help you regain access to your data. All that you should do right now is remove AutoEncryptor from the computer. Moreover, if you have never backed up your data, it is high time you started doing so.
How to remove AutoEncryptor?
AutoEncryptor is a dangerous malware program, with its complex files and processes. Our team at Anti-Spyware-101.com highly recommends that you shield the system from malware threats, including other ransomware infections. Below you will find our instructions which should help you remove the AutoEncryptor Ransomware from the system. If you find that the instructions are too difficult, seek for professional help by implementing a reputable antimalware program. In case of any question, feel free to contact us using the comment box below.
Remove AutoEncryptor Ransomware
- Open Windows Explorer by pressing Win+R.
- Delete unreliable files from the directories Downloads and Desktop.
- Close the window and press Win+R.
- Type in %temp% and press Enter.
- Delete malicious files.
- Delete the files __encrypt.pinfo and UserFilesLocker.exefrom the following directories:
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup\
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup\
- Delete UserFilesLocker.exe from the Desktop and Documents folders.
100% FREE spyware scan and
tested removal of AutoEncryptor Ransomware*





0 Comments.