What is Alex.vlasov@aol.com Ransomware?
It is very easy to identify the malicious Alex.vlasov@aol.com Ransomware because it encrypts files and changes your regular Desktop wallpaper by introducing you to a drawing-type image that displays the same email address. Compared to the warnings of other ransomware, such as Cerber2 Ransomware or VenusLocker Ransomware, this one is very vague. The TXT file created by the ransomware (it is called "How to decrypt your files.txt") does not provide any useful information either. The goal behind these messages is to push you into contacting the provided email. If you do, cyber criminals will know that a system was corrupted successfully, and they will be able to provide you with further instructions on how to decrypt your files. Obviously, the response you will get will push you to pay a ransom, and that is not something you should jump into. Are you rushing to delete Alex.vlasov@aol.com Ransomware? You should stop and think about your next step.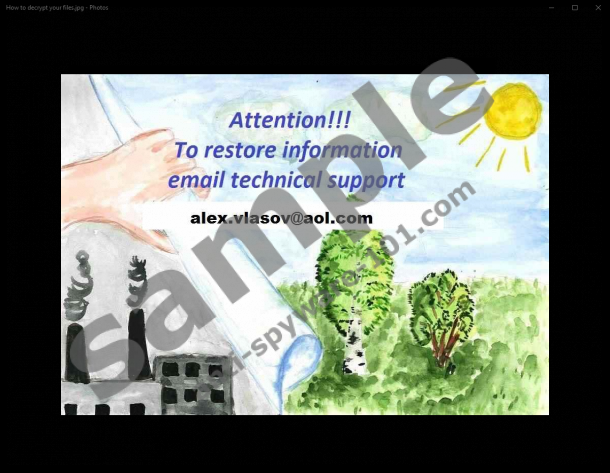

How does Alex.vlasov@aol.com Ransomware work?
Have you already contacted the cyber crooks behind the malicious Alex.vlasov@aol.com Ransomware? These crooks can be reached via the main email address or the alternative one – alex.vlasov@india.com. The “@india.com” email handle can be linked to quite a few different infections, including Green_ray Ransomware, Mahasaraswati Ransomware, and Mobef Ransomware. Have these infections been created by the same malware developer? Although we cannot guarantee this, it is quite possible, especially considering that the messages carried by these ransomware infections are represented in similar ways. If for some reason, the wallpaper on your Desktop is not modified, you should realize that this threat has invaded just by looking at the extension attached to the encrypted files. This extension is “.id-[ID].{alex.vlasov@aol.com}.xtbl” and, besides showcasing the email address, it also lists your ID number. It is most likely that if you contact the email address, you will also be asked to disclose your ID number for identification purposes. Of course, that is if you contact cyber criminals, and we do not recommend that.
The RSA-2048 encryption key used for the encryption of your files cannot be cracked, and this is exactly why the creators of ransomware are so wildly successful. A decryption key created upon encryption is most likely to be sent to a remote server where no one can access it, making the decryption of files impossible. Cyber criminals depend on your need for this key to get your money, but it is difficult to say whether or not they would actually decrypt your files after the payment was received. This is the main reason why we simply cannot advise paying the ransom. Moreover, you should exhaust all other possibilities before you resort to the riskiest of them, which is paying the requested fee. Did you know that legitimate file decryption tools exist? Although in most cases, these tools are unable to crack the encryption by ransomware, it is worth giving a try. You should not even look at any other options if you have your files backed up, and they can be easily accessed, in which case, you should simply replace the infected copies of your files. Of course, you should do that only after you remove Alex.vlasov@aol.com Ransomware. Have you already paid the ransom and your files were actually unlocked? Even if everything seems back to normal, you must delete the ransomware.
How to delete Alex.vlasov@aol.com Ransomware
As soon as you discover Alex.vlasov@aol.com Ransomware on your PC, you need to check which files were encrypted by this malicious infection. If you find out that the most sensitive files encrypted by this threat are backed up, you are unlikely to worry about the loss of other, less meaningful files. Of course, if you want to decrypt all files, you must be looking for a way to crack the encryption. Our researchers advise looking into other ways to decrypt files instead of paying the ransom requested right away. Maybe you will find a legitimate decryptor that will help you out. Maybe a master decryption key will be released (unlikely). Whatever you do, make sure you exhaust all other options before turning to the ransom. Keep in mind that your files might remain encrypted when you pay the ransom. When it comes to the removal of Alex.vlasov@aol.com Ransomware, we advise using an anti-malware tool that will automatically erase malware and keep all threats away from your PC in the future. If you must, you can use the manual removal instructions below, but be careful.
Removal Instructions
N.B. the “*” indicates a random name of the file that you need to remove.
- Tap Win+E keys at the same time to open the Explorer window.
- Delete the *.exefile in the following directories:
- %APPDATA%
- %ALLUSERSPROFILE%\Start Menu\Programs\
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\
- Tap Win+R keys to launch RUN.
- Type regedit.exe into the dialog box and click OK to access the Registry Editor.
- Go to HKCU\Control Panel\Desktop.
- Right-click and Wallpaper value and select Modify.
- Empty the value data box and click OK.
- Go to HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Wallpapers.
- Right-click and BackgroundHistoryPath0 value and select Modify.
- Repeat step 7.
- Go to HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run.
- Right-click and the value with a random name and click Delete (value data: C:\Users\user\AppData\Roaming\*.exe or %AppData%\*exe).
tested removal of Alex.vlasov@aol.com Ransomware*





0 Comments.