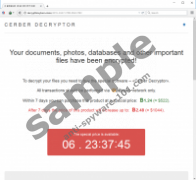
Cerber Ransomware is a devious Windows infection that enters your operating system using clandestine methods. Whether this program slithers in via a corrupted spam email attachment or gets downloaded by a malicious installer, it will hide itself until all of your personal files are encrypted. If this malicious infection successfully encrypts your personal files, it can proceed to demand a ransom from you. According to our research, at the moment, this ransom is 1.24 BTC, which is around 507 USD or 463 EUR. Every user is given 7 days to make the payment, and, if the payment is not made, the ransom supposedly rises to 2.48 BTC (~1014 USD/925 EUR). Note that the Bitcoin currency is quite unstable and the currency ratios fluctuate frequently. All in all, the sums are high, and it is unlikely that many victims have this kind of money lying around. Unfortunately, at the moment, it is impossible to decrypt personal files in other ways, which means that paying the ransom might be the only way to regain control over your files. Of course, this does not change the fact that you must remove Cerber Ransomware. Read more »
SmartStreamSearch
SmartStreamSearch is not so smart. In fact, it is pretty dumb, considering how useless it is. Does it offer streaming? It does not. Does it offer a streaming-related search? It does not. Does it offer any kind of search service? That is debatable, but our team at Anti-Spyware-101.com has found that the extension redirects to a third-party search engine rather than produce its own search results, and that means that it does not actually offer a search service. In fact, this extension does not offer anything, and that is one reason why it is known as a PUP – potentially unwanted program. Another reason is that this extension performs certain actions silently, and these actions are questionable. For one, the PUP can collect PII (personally identifiable information). Also, it can share that PII with undisclosed parties. Are you ready to delete SmartStreamSearch? We are sure that you are. Read more »
Omfl Ransomware
If you leave your Windows system unprotected, Omfl Ransomware is one of the many threats that could invade it. The cybercriminals behind this malware do not even need to put too much effort into executing this malware. They usually send spam emails containing malicious links and attachments to random people, and if they are tricked into clicking on these links and attachments, malware can be executed without anyone’s notice. Obviously, security software should identify and remove malware before it is executed, but there are still plenty of unprotected systems for cybercriminals to exploit. Unfortunately, there are also tons of other threats that can do the same. So, do you need to delete Omfl Ransomware? If you do, we can show how to do it quickly and completely. If you are trying to protect your system against this malware, we can show you how to do that as well. Read more »
OnlineSportsSearch
You would think that OnlineSportsSearch is somehow capable of providing searches specifically for sport-related search queries, but that is not the case. This extension is a PUP – potentially unwanted program – and its main tasks involve hijacking the default search provider, redirecting to Yahoo Search, injecting sponsored links/ads, and also recording information about users and their interactions. Anti-Spyware-101.com researchers recommend removing OnlineSportsSearch from Google Chrome, and you might have already figured out that you want to do exactly that. However, if you would like to learn more about the suspicious extension and the different methods that can be employed to delete it, we suggest that you read this report. If questions remain unanswered for you, add them to the comments section. Read more »
NetGameSearch
Do not waste your time with extensions like NetGameSearch because they cannot offer you anything that you want or need. Did you install this potentially unwanted program (PUP) on a whim? If that is the case, you probably have no reservations about removing it from your Google Chrome browser. However, if you thought about installing it, and you are still convinced that it can be useful, we suggest that you read this report. Our experienced Anti-Spyware-101.com researchers have thoroughly inspected the PUP, and we can explain why its elimination is recommended. Are you looking for instructions that will help you delete NetGameSearch right away? These are provided below, but note that there are other methods of PUP removal that we should discuss. If you do not find the information you are after in this report, we can answer your questions personally. Add them to the comments section below. Read more »
Igdm Ransomware
Igdm Ransomware is a malicious computer infection although you probably do not need this introduction if you’re reading this entry, right? You’re looking for ways to terminate this program, and you found the right page. The manual removal instructions are right at the bottom of the page, although we would strongly recommend acquiring a reliable antispyware tool that would delete Igdm Ransomware and all the other malicious files from your computer at the same time. You just need to make sure that similar programs do not enter your system again. Read more »
GetSearchConverter
Do you have GetSearchConverter installed on your Google Chrome browser? If you do, we have some information for you about this potentially unwanted program (PUP) and why we recommend deleting it as soon as possible. If you do not have this extension installed, but you have encountered its installer, and you are curious to learn if it can offer you something useful, let us warn you that it has nothing to offer. Yes, it sounds like a tool for better web searches, but that is just a disguise that hides highly suspicious activities. Our team of experts at Anti-Spyware-101.com strongly recommends removing GetSearchConverter if it is installed and refusing it if it is offered for installation. We go deeper into these topics in this report, but if you feel like you know enough already, and you want to get to the removal part, check out the last section. Read more »
Mifr Ransomware
Did you think that your Windows operating system was secure prior to the invasion of Mifr Ransomware? If you did, you must have changed your mind because if a system is protected appropriately, malware shouldn’t be able to slither in. Unfortunately, this ransomware is not one of the threats that you can remove and escape all consequences. It encrypts all personal files, and that does not change once you delete Mifr Ransomware. Of course, that should not deter you from eliminating this dangerous malware, and if you have no idea as to how to even approach the task, we strongly advise that you keep reading this report. Our Anti-Spyware-101.com research team has recently analyzed the threat thoroughly, and we know what the best way to get rid of it is. As always, we have the comments section opened, and you can add your questions for our team to address. Read more »
Leitkcad Ransomware
Do you think about malware, like Leitkcad Ransomware, as soon as you turn on your computer? Hopefully, you do because you can never be too safe when it comes to malware. Unfortunately, many of our daily routines are exploited by cybercriminals, who are constantly trying to execute malicious infections. For example, malware could hide in flash drives, emails, downloaders, and even on social media platforms. The thing is that attackers need to be creative when it comes to malware distribution, and that is why you can never let your guard down. Obviously, if you take certain security steps, you can minimize your chances of facing threats greatly, and that is what we discuss in this report. We also show how to delete Leitkcad Ransomware in case it manages to slither into your Windows operating system. Note that this malware must be removed as soon as you discover it, but your files might be damaged permanently. Read more »
Quick Clear Cache
Google Chrome users can download Quick Clear Cache for free from the Chrome Web Store. Its installer exists at chrome.google.com/webstore/detail/quick-clear-cache/badahmnhfpinlghdjjlpedolagbfefoe. However, just because something is available to you, that does not mean that it is helpful or reliable. Our Anti-Spyware-101.com researchers have analyzed the extension, and the conclusion is that it is neither useful nor reliable. Therefore, it is classified as a potentially unwanted program. Note that we use the abbreviation ‘PUP’ throughout this report. It is important to note that PUPs are not always incredibly malicious, and not all security tools identify them as threats either. That said, if you continue reading this report, you will understand the reasons why our team suggests deleting Quick Clear Cache. If you do not agree with our fact-based opinions, or you want to discuss certain things further before you decide whether or not to remove the extension, note that you can use the comments section below to contact us. Read more »
IncognitoSearchPro
Did you seek out IncognitoSearchPro, and you installed it because it seemed to offer exactly what you were looking for? That is unlikely to be the case, given that this extension does not really offer much. It simply states that it can optimize search results represented via Yahoo Search, and you can find this statement at chrome.google.com/webstore/detail/incognitosearchpro/jjenlgjplfbkcblajicehijdofcnamij. We doubt that many users would think to install a tool to make their search results better because that is not really a legitimate service. If you were not pleased with your search tool, it is more likely that you would switch it for something else rather than look for ways to enhance it. In any case, we suggest that you delete IncognitoSearchPro if you have downloaded it onto your Google Chrome browser. Of course, we do not recommend removing it just because we doubt that anyone would be interested in it. There are serious reasons why eliminating this extension is advised. Read more »